General Scanners
| < Day Day Up > |
| A vulnerability scanner performs the following steps:
The sections that follow cover five popular vulnerability scanners:
NessusNessus (http://www.nessus.org) is an open-source vulnerability scanner created by Renaud Deraison in 1998. Originally a Linux tool, there is now a Windows version. Nessus is free to use under the GPL, but it does require an activation key, which is sent to a validated e-mail address. This validation helps track who is using the tool, which might deter some malicious hackers from using Nessus. Nessus is a powerful scanner with its own scripting language called Nessus Attack Scripting Language (NASL). Nessus scans your target for standard ports but also checks nonstandard ports for services. For example, if you have a web server running on port 8080 instead of port 80, Nessus is powerful enough to detect this by checking each port, not just the common ports, for common services such as web and FTP. Nessus has more than 7600 plug-ins available for downloading. Reports are done through a secure web interface. You can generate your own web certificate through the nessus-mkcert utility or import one from a trusted certificate authority. Certificates help to secure the web interface by both verifying the authenticity of the server and providing encrypted communications between the web browser and the Nessus server. Before you use Nessus, create a user using the nessus-adduser utility. You can even specify which hosts a user is allowed to scan. This way, you can prevent users from mistakenly (or intentionally) scanning unauthorized hosts. Figure 13-1 shows an example of a Nessus report. Figure 13-1. Sample Nessus Report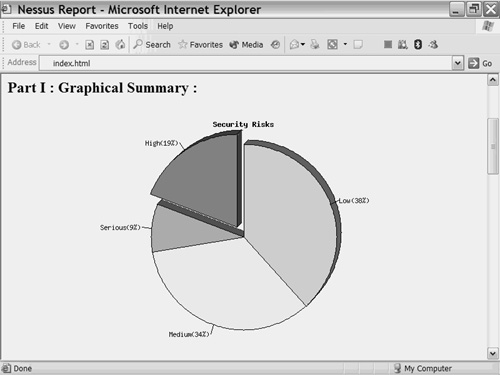 Tip If you use the Linux version of Nessus you will need to install uudecode which is part of the sharutils suite. You can obtain this from http://www.gnu.org/software/sharutils/sharutils.html. SAINTSecurity Administrators Integrated Network Tool (SAINT) is available through the SAINT Corporation at http://www.saintcorporation.com/products/saint_engine.html. SAINT is a commercial scanner based on SATAN, an older vulnerability scanner developed by Dan Farmer and Wietse Venema in 1995 (http://www.porcupine.org/satan/). Although SAINT was originally designed for Linux, it is now available on SunOs 5.6/Solaris 2.6, HP-UX 11.00, FreeBSD, and MacOS. As a penetration tester, companies often employ you to test a target for compliancy with federal regulations, such as the Graham-Leach-Bliley Act (GLBA) and the Health Insurance Portability and Accountability Act (HIPAA). (See Chapter 2, "Legal and Ethical Considerations," for more about these regulations.) SAINT demonstrates compliance with these and other federal regulations. SAINT even supports scheduled scans so that you can arrange routine scanning for regulatory compliance. If cost is an issue, you can opt for the WebSAINT option. This is a paid service performed across the Internet where you pay for a subscription with the SAINT Corporation. Results are sent back to you via e-mail. Tip For best operation, it is recommended that you have the following utilities installed when running SAINT:
Also, turn off TCPd wrappers, because this causes inaccurate results. SARAThe Security Auditor's Research Assistant (SARA) is an open-source scanner released under GPL by the Advanced Research Corporation (http://www-arc.com/sara/). Sara is available on Linux, UNIX, Mac, and on Windows using Cooperative Linux (http://www.colinux.org), a distribution of Linux that runs on top of Windows. SARA checks for the SysAdmin, Audit, Network, Security (SANS) Institute top 20 vulnerabilities and supports the Common Vulnerabilities and Exposures (CVE) standards (http://cve.mitre.org). SARA updates itself twice a month and downloads the latest vulnerabilities. SARA does not test for DoS vulnerabilities, which makes it safe to test on corporate networks. However, older systems might still crash during some tests, so make sure all parties are aware that although a DoS attack will not intentionally be performed, it is still possible for one to occur inadvertently. Figure 13-2 shows a sample SARA report. Figure 13-2. Sample SARA Report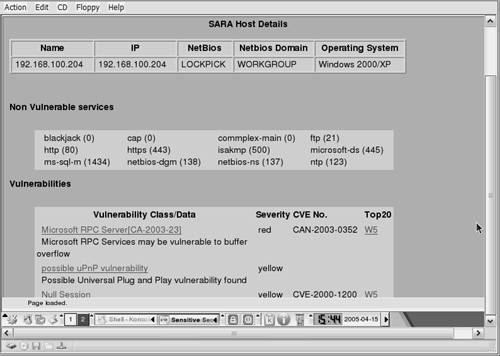 You can export reports in spreadsheet, XML, or Microsoft Word format. SARA categorizes the seriousness of detected vulnerabilities by color, as shown in Table 13-1.
Like SAINT, SARA supports scheduled scans. You can perform these scheduled scans through the command line or by modifying the timing rules in the sara.cf file. You manage SARA in three ways:
ISSThe Internet Security Scanner (ISS) is a Windows-based commercial scanner available at http://www.iss.net that has rich reporting features. ISS provides three different reports, depending on the level of detail needed:
Example 13-1 shows a sample technical report. Example 13-1. Sample ISS Technical ReportIP Address {DNS Name} Operating System 172.16.1.2 {HMN}Cisco IOS C2900XL-H2-M accountblankpw: User account has blank password (CAN-1999-0504) Additional Information More Information vlb An account has been detected with a blank password. Some vendors ship Windows NT pre-installed with a blank password on the Administrator or other user accounts. This misconfiguration is an extremely high risk vulnerability, and should be corrected immediately. This vulnerability is typically detected on a computer where there is also no minimum password length required. If the Guest account has a blank password, it allows anyone to log in with any username and a blank password. If the file and registry permissions are not very tightly restricted, this situation can give any attacker the ability to access sensitive information and systems. Internet Scanner users: This check finds local and domain accounts that are part of the Domain Users group. Any local account found that is part of a non-Windows built- in group will also appear vulnerable. Enabling this check automatically enables password checking in the NT Logon Sessions common settings. If no password checking method is specified, then the method defaults to 'Check Accounts by Logon,' otherwise the method(s) selected by the user takes affect. The password-checking source 'Use Blank Password' is then enabled in addition to any sources selected by the user.NetReconNetRecon is a Windows-based commercial scanner from Symantec (http://www.symantec.com). NetRecon includes a patent-pending progressive scanning technology that scans hosts in parallel and adapts its penetration strategy based on previously gathered results. NetRecon is unique in this sense as it actively learns and adapts to the environment it is testing. For example, if it is able to crack a password on one system it will remember that password and attempt it on other systems. |
| < Day Day Up > |
EAN: 2147483647
Pages: 209