Encrypting File System (EFS)
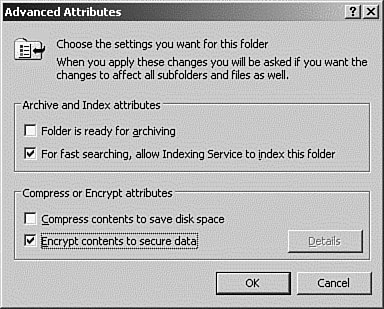
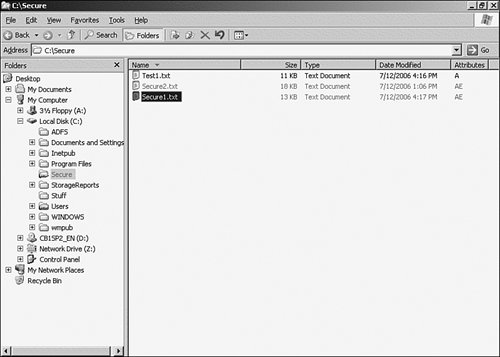
| One of the hot items in the news lately has been data theft. There have been far too many cases of thieves either accessing sensitive data over the Internet or stealing laptop computers that contain thousands of names, Social Security numbers, bank account numbers, and the like. Too many people assume that as long as an asset is password protected that their data is safe. This is far from the case. Any amateur with a password-cracking program can gain access to a computer, and accessing data from a stolen computer is as simple as installing a new operating system on the hard drive, or just adding the hard drive to another computer. After files are accessed, they can be read or copied. The Encrypting File System (EFS), first introduced in Windows 2000, has been updated for Windows Server 2003. EFS is an extension to NTFS and provides file-level encryption. EFS uses public/private key technology, which makes it difficult, but not necessarily impossible, to crack. As is typical with this key technology, the public key is used to encrypt the data, and a private key is used for decryption. The public key is just thatpublic. It can be passed around and is used to encrypt a file or an email message. Public keys are good for information exchange, such as secure mail. A user can publish her public key, and people can use this key to encrypt any mail they are sending to her. They can be assured that no one else can read the message, because it can be decrypted and read only by using the private key, which is kept secure by the receiver. Exam Alert: Public/Private Key Technology This technology is covered at length on the 70-298 Designing Security for a Microsoft Windows Server 2003 Network exam. More information about this technology can be found at http://windowssdk.msdn.microsoft.com/en-us/library/ms732314.aspx. Encryption in EFS works by using a public/private key pair with a per file encryption key. When a user encrypts a file, EFS generates a file encryption key (FEK) and uses the public key to encrypt it. When the user wants to read or decrypt the file, the FEK is decrypted using the private key. The FEF is used to decrypt the file. Note: The file encryption and compression attributes are mutually exclusive. You can apply one or the other to a file, but not both. Although you can mark a folder as encrypted, the folder itself is not actually encrypted. EFS provides only file-level encryption. By marking a folder as encrypted, any files that are created or moved into the folder are automatically encrypted. Any existing files in the folder at the time that you set the encryption attribute are not automatically encrypted unless you select the option to apply changes to the folder, subfolder, and files on the Confirm Attribute Changes dialog. The first time a user selects the encryption attribute from the properties dialog box of a file or folder, EFS will automatically generate a public key pair; then the private key is certified by a Certificate Authority (CA). If a CA is not available, the public key is self signed. All this is transparent to the user. In Step by Step 13.17, we will use EFS to encrypt a folder, create a file in that folder, and then copy a file to that folder to see the effects of the encryption process.
As you saw in the exercise, turning on encryption for a file or folder is pretty simple. In addition, after encryption is turned on for a folder, every file that is created or moved into that folder is automatically encrypted, without any user intervention. Any existing files are not affected. The following conditions apply when moving or copying encrypted files:
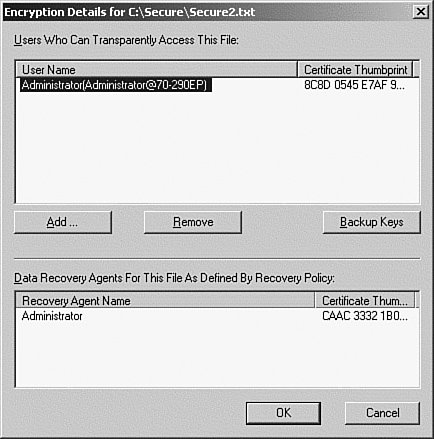
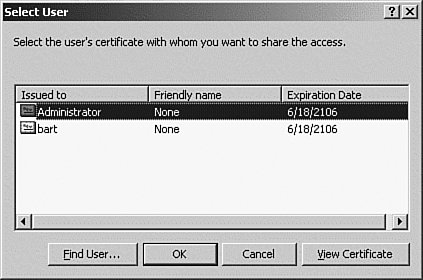
After encryption is configured, the encrypt/decrypt process is transparent to the user and to applications. When a user opens a file, it is automatically decrypted and will be reencrypted when the user saves it. Because encryption is a file-level process, the application is unaware that it is working with an encrypted file. However, you must be careful to set the encryption attribute on for the folder that the file is stored in, because some applications, such as Microsoft Word, will create temporary files, and they will not be encrypted unless they are in an encrypted folder. Sharing Encrypted FilesIn some situations, the data in a file will need to be shared with other users, or possibly a group of users. However, it will still be important to keep the contents secure. In this situation, you can specifically share the encrypted file with other users. However, keep the following points in mind:
Note: Certificate Required As we mentioned earlier, all users that are being granted access must have a certificate. The easiest way to get a certificate is to encrypt a file or folder, which will automatically generate an EFS certificate for that user. To share an encrypted file, follow the procedure in Step by Step 13.18.
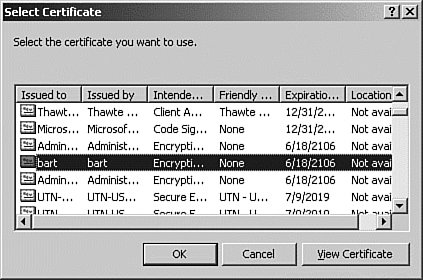
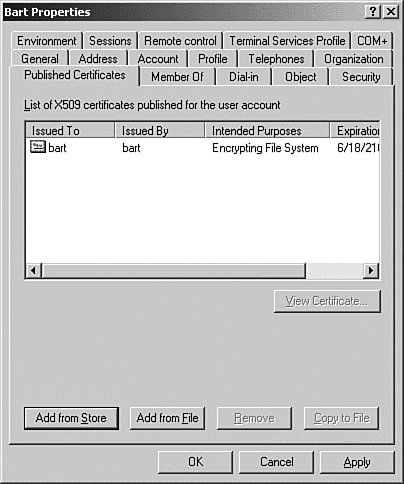
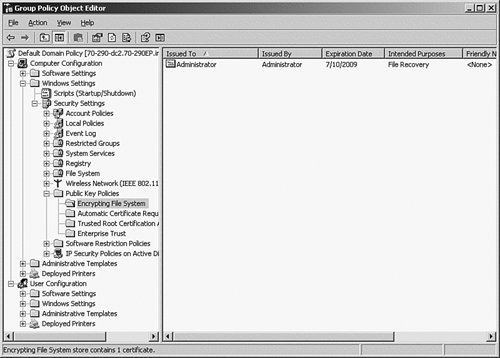
EFS Recovery AgentsSo how can encrypted data be recovered if users lose their private key or leave the company? On standalone Windows servers and workstations (not members of a domain), the Data Recovery Agent (DRA) role must be manually assignedit is not created automatically. In a domain, the domain administrator's account will automatically be granted this role. Because this account is designated as the DRA, a recovery key is generated and saved in the local administrators' certificate store that can be used by the local administrator to recover the encrypted data. This recovery key can be used only to recover the data. The user's private key is never revealed. If the DRA role is removed by a configuration error, the system assumes that no data recovery policy is in place and will refuse to encrypt any files or folders. Note: The user account with recovery agent rights will be able to copy the file to his/her computer to perform recovery operations. Any user can be a recovery agent; no other rights are required. Creating a Domain DRAAfter a user has encrypted a file, an EFS certificate is automatically created for them. This certificate is needed before the user can be designated as a recovery agent. In the following Step by Step, we will perform the two steps needed to create a DRA: First, publish the certificate to the user account, and then add the user account as an EFS Recovery Agent.
Recovering an Encrypted File or FolderTo recover an encrypted file or folder, the recovery agent must copy the file to his computer, if in a domain, or log on to the computer with the local administrator account on a standalone computer. To recover a file or folder, follow these steps:
If the computer is a member of a domain, move the file back to the user's computer. Encryption Using the Cipher CommandThe cipher command-line utility is supplied so that you can work with encrypted files and folders from the command line. This is handy when you are encrypting or decrypting a large number of files or folders, because you can use wildcards or run the utility from a script. The cipher command options are listed in Table 13.2.
Exam Alert: You might encounter EFS questions on the exam. You should know how to encrypt and decrypt files and folders using both the GUI and the cipher utility. In addition, you should be familiar with the key recovery process. |
EAN: 2147483647
Pages: 219