Lesson 2: Designing Remote Access Security for Users
You can apply several settings to secure user connections to the network. These settings include user properties that allow or deny remote access, authorization based on the source or destination phone number, and preconfigured remote access connection objects using the Connection Manager Administration Kit (CMAK).
Planning User Settings for Dial-Up Networking Security
Windows 2000 allows an administrator to configure how dial-up security is applied at the user account property level, as shown in Figure 13.5.
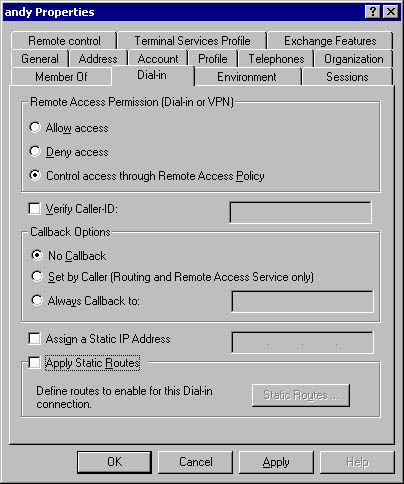
Figure 13.5 Dial-in properties for an Active Directory user account
For each user account you can define the following settings to secure remote access connections:
- Remote Access Permission. You can set permissions for each user to allow access, deny access, or control access through remote access policy. Even if allow access is selected, remote access policy will be evaluated to ensure that the connection attempt matches the defined profile settings.
- Verify Caller-ID. If caller ID is implemented on the phone system, the phone number from which the remote access connection originated can be verified against this attribute value. If the originating phone number doesn't match, the connection attempt is dropped.
- Callback Options. Callback allows phone charges to be applied to the remote access server rather than to the remote access client. You can choose to implement no callback security, have the remote access client provide the phone number to call back, or require callbacks to predetermined phone numbers. Configuring callback to call a specific number provides the highest form of security.
- Assign a Static IP Address. Some firewall software identifies connections by their IP address. Use the static IP address attribute to assign a specific IP address to a client connection. This attribute requires that the remote access client always connects to the same remote access server. If the connection is made to a remote access server on a different network, the IP addressing could be incorrect.
- Apply Static Routes. You can restrict which networks a remote access client can access by applying static routes to the remote access connection. If a network segment isn't included in the static routes, access to that segment of the network is prevented.
Making the Decision
When designing remote access security, you want to include user property settings to secure remote access connections, as described in Table 13.5.
Table 13.5 Planning User Properties for Remote Access
| To | Set the Following User Property Settings |
|---|---|
| Prevent remote access to the network | Configure the remote access permission for the user account to Deny Access. |
| Use remote access policy settings to determine remote access permissions | Configure the remote access permission for the user account to Control Access Through Remote Access Policy. |
| Restrict dial-up connections to a specific phone number | In phone networks that support caller ID verification, configure Verify Caller–ID to the approved phone number. In phone networks that don't support caller ID verification, configure the callback number to a specific phone number. Be careful with this option, because call forwarding could forward the callback to an unauthorized phone number. |
| Assign a specific IP address for all connection attempts by the user | Set the Assign A Static IP Address attribute to the required IP address. Ensure that the remote access client connects only to a single remote access server or to remote access servers on the same network segment. |
| Restrict remote access clients to specific network segments | Define static routes for the remote access client that define which network segments are accessible by the remote access client. |
In addition to configuring individual attributes of a user account to secure remote access, you can also enable the remote access account lockout feature at the remote access server. Remote access account lockout denies remote access to a user account if a preconfigured number of failed authentication attempts occur during remote access connections. This setting helps prevent an attacker from attempting dictionary attacks over a remote access connection. The attacked account will be disabled for remote access once the number of failed attempts exceeds the configured threshold.
NOTE
Remote access account lockout isn't related to user account lockout. Remote access account lockout only prevents an account from connecting to the network using remote access. Account lockout prevents all access to the network for the locked out account.
You must define two registry settings to enable remote access account lockout:
- Set HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services \RemoteAccess\Parameters\AccountLockout\MaxDenials to set the value for the failed attempts counter. If the counter exceeds the configured value, remote access will be locked out for the account. A successful authentication resets the failed attempts counter.
- Set HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services \RemoteAccess\Parameters\AccountLockout\ResetTime to the interval in minutes that you wish to reset the failed attempts counter to a value of zero. The default for this value is 2880 minutes or 48 hours.
If the remote access server is configured for RADIUS authentication, you must make the registry modifications at the server running Internet Authentication Services (IAS).
WARNING
Enabling the remote access account lockout settings leaves your network susceptible to an attacker. An attacker could lock out user accounts by attempting remote access connections for a user account until the account is locked out.
Applying the Decision
If Hanson Brothers chooses to deploy remote access security by using remote access policies, then the default option of Control Access Through Remote Access Policy is appropriate for all user accounts. If Hanson Brothers wants to ensure that certain accounts, such as the Guest account, can't be used for remote access, those accounts can be configured to Deny Access.
For Adventure Works you should define a dedicated user account for connecting to the Hanson Brothers network. You should configure the dial-in settings for the account to Verify Caller–ID, with the phone number being set to the predefined phone number at Adventure Works. If the calls were long distance, Hanson Brothers could cover the phone charges by using callback security to return the call to the specified phone number. Using both attributes ensures that the call originates at an authorized phone number and that the callback is made to an authorized phone number.
Authorizing Dial-Up Connections
In addition to authenticating remote access connections, you can also implement Windows 2000 remote access authorization techniques. Authorization techniques don't evaluate the account that's attempting the connection but instead examine the attributes of the connection attempt. In fact, it's reasonable to eliminate authentication from the dial-up connection attempt when using authorization methods.
IMPORTANT
To use these authorization methods, the entire phone system must support the authorization method. This includes the telephone system that the caller uses, the telephone system between the caller and the remote access server, and all communications hardware used to complete the call. If any part of the connection doesn't support the authorization method, authorization will fail.
Windows 2000 supports the following remote access authorization methods:
- Automatic Number Identification/Calling Line Identification (ANI/CLI). ANI/CLI restricts a remote access connection to one or more originating phone numbers. If the remote access connection doesn't originate from the configured phone number, the connection attempt is denied.
- Dialed Number Identification Service (DNIS). DNIS identifies the phone number dialed by a remote access client. DNIS allows you to apply different remote access policies based on the phone number dialed by the remote access client. This is useful for organizations such as an ISP that provides different phone numbers to different clients even though all clients call the same modem pool. DNIS allows the ISP to identify which company the client is calling from and applies the correct remote access policy to the client.
What's the Difference Between ANI/CLI and Caller ID?
ANI/CLI doesn't require the remote access connection to provide user credentials. When you use ANI/CLI, the remote access connection is authorized based on the originating phone number. No user credentials are sent in the connection request.
Caller ID is an attribute of a user account. The caller ID attribute isn't verified until after the credentials are presented for a remote access connection.
Use caller ID when you wish to use the Windows 2000 access model to secure access to other resources on the network.
- Third-Party Security Host. You can configure remote access to the network to require the use of a third-party security host such as a SecureID security card. A SecureID security card prevents replay attacks by generating a new access code with each successful connection to the network. If a previous authentication attempt is replayed on the network, it will be using a previous code that's now invalid.
Making the Decision
Use Table 13.6 to determine when to implement authorization methods for remote access connections in a Windows 2000 network.
Table 13.6 Planning Authorization for Windows 2000 Remote Access Connections
| Use | To Meet the Following Security Goals |
|---|---|
| ANI/CLI | To restrict connections to a specific originating phone number. If the phone number doesn't match the configured originating phone number, the connection is dropped. |
| DNIS | To host multiple phone numbers using the same bank of modems. DNIS allows you to create remote access policies based on the telephone number called by a remote access client. |
| Third-party security hosts | Your network requires protection against replay attacks. Unique session keys and access codes must be used for access to a high security network. |
Applying the Decision
Hanson Brothers should consider using a combination of ANI/CLI and DNIS for the connection from Adventure Works. Adventure Works should use a different phone number when connecting to the Hanson Brothers network to query stock levels. DNIS can identify connection attempts to the network and apply the most restrictive remote access policy to the connection.
Alternatively, Hanson Brothers could use ANI/CLI to provide Adventure Works with unauthenticated, but authorized, access to the network. Only connections from the predefined phone number would be allowed to connect. The only problem with using ANI/CLI is that you can't use security for requests to the stocking application. The connection could use only the default security defined for the application because the Adventure Works user wouldn't be required to provide user credentials.
Securing Client Configuration
Dial-up networking for clients requires that the client computers are configured with dial-up connections to the remote network. The configuration and maintenance of dial-up connections objects at the remote access clients can cause administrative overhead if the configuration is modified incorrectly.
The CMAK, which is included with Windows 2000 Server, allows an administrator to create a dial-up networking connection that works with Windows 95, Windows 98, Windows NT 4.0, and Windows 2000. A dial-up network connection object created using the CMAK provides the following advantages over user-defined dial-up networking objects:
- It defines a highly secure connection object. To remove the possibility of weakened security due to a remote access client modifying connection settings, you can define the connection object to block access to key configuration screens.
- It defines a package that launches a dial-up and VPN connection. The combined package simplifies the VPN process by requiring the end user to launch only a single connection object. The package will automatically launch the VPN once Internet connectivity is established.
- It defines a package that works on Windows 95–, Windows 98–, Windows NT 4.0–, and Windows 2000–based computers. The CMAK creates a package that can be deployed to most Windows operating systems.
- It removes saved password vulnerabilities. The CMAK allows you to prevent a user from saving his password within the network connection object.
- It deploys preset security configurations. You can predefine the connection object with the required authentication protocol, tunnel protocol, and encryption levels for both dial-up and VPN connections.
- It uses a standard phone book. You can update the connection object with a phone book that provides current local phone numbers.
Making the Decision
When defining a CMAK package, ensure that the options in Table 13.7 are configured to provide security.
Table 13.7 Configuring CMAK Packages to Secure Remote Access Connectivity
| To | Configure the Following CMAK Package Settings |
|---|---|
| Provide local access numbers | Define a phone book that provides local access numbers for all locations where employees will access the Internet. |
| Simplify the dial-up process when VPNs are deployed | Configure the CMAK package to automatically launch the VPN connection once the Internet connection is established. |
| Prevent modification of security configuration parameters set in a dial-up connection | Restrict access to the property pages where security parameters are configured. Consider including authentication protocols, encryption settings, and tunnel settings when using VPNs. |
| Prevent remote access connections by unauthorized personnel | Configure the CMAK package to prevent users from saving their passwords. This prevents an unauthorized user from connecting to the corporate network. |
| Meet multiple dial-up configuration requirements | Configure separate CMAK packages to match each dial-up configuration required. |
Applying the Decision
Hanson Brothers can create a CMAK package that preconfigures desired settings to allow remote employees to connect to the office network. You can create separate CMAK packages for both the dial-up and VPN clients. Table 13.8 outlines the settings that you could design for the dial-up and VPN client CMAK packages.
Table 13.8 Designing CMAK Packages for Hanson Brothers
| CMAK Package | Recommended Settings |
|---|---|
| Dial-up clients | Configure the phone book to provide local access numbers for the Calgary, Boise, and Warroad offices. Configure the dial-up connections to use only MS-CHAPv2 to ensure mutual authentication of remote access client and remote access server. Configure the dial-up connections to require the strongest encryption settings. Prevent access to the Security tab to prevent users from modifying data encryption or authentication settings. |
| VPN clients | Configure the phone book to provide host names for the remote access servers at the Calgary, Boise, and Warroad offices or configure separate CMAK packages for each office. Configure the VPN connections to only use MS-CHAPv2 to ensure mutual authentication of remote access client and remote access server. Configure the VPN connections to require the strongest encryption settings. Configure the VPN connection to use only PPTP. Before implementing L2TP/IPSec connections, you must deploy computer certificates to all remote access client computers. Prevent access to the Security tab so users can't modify data encryption or authentication settings. |
Lesson Summary
Your remote access security design defines whether it's more appropriate to allow connections based on user account or on phone number information. You can use a combination of the two, but be careful to make sure that the criteria are reasonable so that the appropriate users can access the network.
Finally, the CMAK lets you control the security settings of remote access connections by enforcing the settings that your organization requires and allowing you to restrict access to key configuration screens for the remote access connection objects. This ensures that the desired level of security is used for all remote users accessing the network.
EAN: 2147483647
Pages: 172
- Chapter I e-Search: A Conceptual Framework of Online Consumer Behavior
- Chapter IV How Consumers Think About Interactive Aspects of Web Advertising
- Chapter X Converting Browsers to Buyers: Key Considerations in Designing Business-to-Consumer Web Sites
- Chapter XVI Turning Web Surfers into Loyal Customers: Cognitive Lock-In Through Interface Design and Web Site Usability
- Chapter XVIII Web Systems Design, Litigation, and Online Consumer Behavior