Sniffing the Network
Whether or not you have secured your WLAN, with wireless networks, it’s not easy to predict the propagation of radio waves. Radio waves do not travel the same distance in every direction because obstacles such as walls, people, and land formations create attenuation, or weakening of the Wi-Fi radio signal. Because of this, many wireless networks are susceptible to attack by wardrivers using sniffer software and equipment.
| Cross-Reference | I discuss placement of WLAN equipment and dealing with interference issues in Chapter 8. |
Sniffers are available in many flavors, and most of them are free software down- loads for anyone to install and use. People can use sniffers to detect and map out your WLAN, but also to capture data and even crack your encryption.
| Cross-Reference | I discuss weaknesses of Wi-Fi encryption in Chapter 10. |
Sniffers are available for most operating systems, including handheld pocket PC devices, and even sniffing for WLANs using a keychain Wi-Fi seeker gadget (see Figure 5-6).

Figure 5-6: You can use devices like the Chrysalis WiFi Seeker to sniff out WLANs.
How sniffing works
Although you have likely heard the argument that nobody owns the airwaves, wireless sniffing is a form of electronic eavesdropping. Essentially, to determine the location of a WLAN and if that WLAN has security precautions in place, an intruder using a Wi-Fi network card, and some free sniffing software can roam until he identifies a signal. By analyzing its strength, he can alter his geographic position until he finds the target access point (see Figure 5-7).
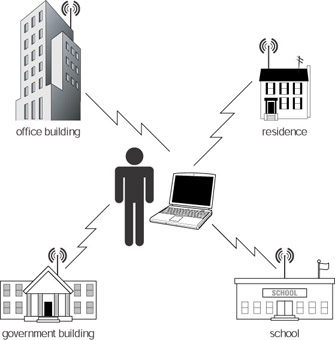
Figure 5-7: Roaming for targets
Some of the sniffing software that an intruder uses can also capture passwords, unencrypted data, and even aid in cracking encrypted data. Because wireless communications are accessible to anyone connected to or within range of the WLAN, sniffing is the most effective technique in wireless attacks.
The promiscuous NIC
Typical sniffers are software programs that passively intercept and copy all traffic that passes by the system’s wireless network interface card (NIC). Most sniffers are used for legitimate functions such as network monitoring and troubleshooting. Sniffers are an invaluable tool for diagnosing network problems during communication hosts and nodes. A sniffer captures the data coming in and/or going out of the NIC and displays that information in a table. Some sniffers can even take that a step further by analyzing the data and looking for potential security weaknesses and other network problems.
To do this, sniffers place NICs into a monitoring state called promiscuous mode. The term implies that the NIC does not have to participate in the network or send packets and, therefore, can passively eavesdrop and capture data unnoticed. This is like a hidden wiretap that allows third parties to listen in on network transmissions. For this reason, sniffers can wreak havoc on a secure network because they are almost impossible to detect.
| Note | Wireless sniffers are powerful tools that you can use to audit and defend a WLAN as well as attack it. Because sniffing is usually a passive activity there is little you can do to detect and prevent it. Your best defense is to refer to Chapter 11 and follow the steps for securing your WLAN, and Chapter 10 for best practices regarding Wi-Fi encryption. |
EAN: 2147483647
Pages: 145
- Chapter V Consumer Complaint Behavior in the Online Environment
- Chapter IX Extrinsic Plus Intrinsic Human Factors Influencing the Web Usage
- Chapter XII Web Design and E-Commerce
- Chapter XVI Turning Web Surfers into Loyal Customers: Cognitive Lock-In Through Interface Design and Web Site Usability
- Chapter XVII Internet Markets and E-Loyalty