3-Tier Architecture
This is modeled after a large, commercial web server farm. A real web farm would have multiple application servers and multiple databases, but that would just clutter up this example. To add additional servers, just duplicate what exists here and rename the macros.
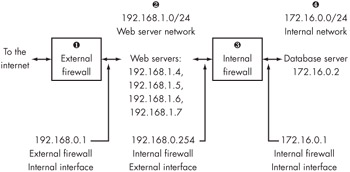
Our 2 application tier is protected from the Internet by a very restrictive set of 1 firewall rules. The only access to the application servers in this environment is on port 80 and 443, plus SSH from a management network. The application servers are not allowed to initiate outbound connections to the Internet, and are are load-balanced so that if one fails it can be removed from the pool without affecting service level agreements. This technique is very popular with Windows web servers in high-availability environments; when you have to reboot a server, just pull it from the load balance pool until you're done.
Most large-scale application servers get their data from a 4 database server. The database server is protected from the application servers by a 3 second firewall that only allows database queries and our management SSH connection from the outside world. Note that the application servers are not allowed to SSH to the database tier; if an intruder successfully compromises a web server, they still cannot stage an attack against the database server except through a very small window. While they can make database queries, anyone who has ever tried to reverse-engineer a complicated database will tell you that this is quite difficult without documentation! This design is quite efficacious against would-be intruders.
In some three-tier network environments, the application servers will have two network cards; one facing the Internet firewall, and one facing the database tier. Not only does this improve performance on the local Ethernet, it also slightly enhances security.
This type of network requires proper routing, which we discussed in Chapter 5 — in fact, we routed this exact example in Chapter 5! We also need configuration files for both the application server firewall, and the database tier firewall.
# Application Tier Firewall Configuration #set our macros ext_if = "fxp1" int_if = "fxp0" ext_ip = "209.69.178.26" int_ip = "192.168.1.1" ext_net = "209.69.178.16/28" int_net = "192.168.1.0/24" db_net = "172.168.0.0/24" mgmt_net = "209.69.178.18/32" #also use macros for our load-balanced application servers appservers = "{ 192.168.1.4, 192.168.1.5, 192.168.1.6, 192.168.1.7 }" #normalize all traffic we receive and transmit scrub in all #use NAT so we can access internal equipment, such as switches, from #the outside world. nat on $ext_if from { $db_net, $int_net } to any -> $ext_ip #here, we load-balance our application servers rdr on fxp1 proto tcp from any to $ext_ip port { 80, 443 } -> $appservers # block in log all #allow traffic from the world to our application server pass in on $ext_if proto tcp from any to $appservers port { 80, 443 } keep state #allow packets from our management network (a single IP, in this case) to #enter the network pass in on $ext_if proto tcp from $mgmt_net to { $db_net, $int_net } keep state #lastly, make sure we are spoof-protected antispoof for $ext_if antispoof for $int_if # Database Tier Firewall Configuration #set our macros ext_if = "fxp1" int_if = "fxp0" ext_ip = "192.168.1.254" int_ip = "172.16.0.1" ext_net = "192.168.1.0/24" int_net = "172.16.0.0/24" mgmt_net = "209.69.178.18/32" #our database server dbserver = "172.16.0.2" #normalize all traffic we receive and transmit scrub in all #Our application tier firewall is doing NAT for us, so we do not need #to NAT further... #...but we do need to filter traffic block in log all #allow traffic from the world to our application server #Port 1723 is used by the Oracle listener; each database has its own port~ pass in on $ext_if proto tcp from $ext_net to $dbserver port 1521 keep state #allow packets from our management network (a single IP, in this case) to #enter the network pass in on $ext_if proto tcp from $mgmt_net to $db_net, $int_net keep state #lastly, make sure we are spoof-protected antispoof for $ext_if antispoof for $int_if EAN: 2147483647
Pages: 298
- ERP Systems Impact on Organizations
- Enterprise Application Integration: New Solutions for a Solved Problem or a Challenging Research Field?
- Context Management of ERP Processes in Virtual Communities
- Distributed Data Warehouse for Geo-spatial Services
- Healthcare Information: From Administrative to Practice Databases