4.2 The WMI security configuration
4.2 The WMI security configuration
Any manageable object we discussed in the previous chapters can be accessed under some security conditions. The WMI access is defined by three methods:
-
During the WMI connection, the entity accessing a system must provide an authentication method and some privileges to perform specific tasks (i.e., system reboot) or access some specific manageable objects (i.e., security event log).
-
The entity accessing the manageable object is granted access to a CIM repository namespace and allowed to perform some specific operations. The entity in question could also be part of an authorized group.
-
The manageable object is restricted in access in a namespace by the means of a security descriptor. A security descriptor is nothing other than a representation, in the form of a list, of the access rights granted or denied to entities for the purpose of accessing a secured object in the system.
4.2.1 The WMI connection security settings
The establishment of a WMI connection always includes an authentication method, an impersonation level, and some optional privileges definition. Throughout the first book, Understanding WMI Scripting, we talk about this aspect when we explain how to perform a WMI connection. You can refer to Chapter 4 of the first book, sections 4.3.3, "The security settings of the moniker," and 4.1, "Establishing the WMI connection," for more information about the WMI connection scripting technique and the various connection settings.
However, it is important to determine the type of privileges required for a specific WMI operation. Table 4.1 lists the WMI classes that require some specific privileges at the class level, the property level, or the method level.
| Namespace | WMI Class | CIM Element | Name | Privileges | Description | |||
|---|---|---|---|---|---|---|---|---|
| ROOT/CIMV2 | Win32_PageFileUsage | Class | SeCreatePagefilePrivilege | The Win32_PageFileUsage class represents the file used for handling virtual memory file swapping on a Win32 system. Information contained within objects instantiated from this class specify the runtime state of the page file.
| ||||
| ROOT/CIMV2 | Win32_Process | Property | ExecutablePath | SeDebugPrivilege | The ExecutabtePath property indicates the path to the executable file of the process. | |||
| Property | MaximumWorkingSetSize | SeDebugPrivilege | The MaximumWorkingSetSize property indicates the maximum working set size of the process. The working set of a process is the set of memory pages currently visible to the process in physical RAM. These pages are resident and available for an application to use without triggering a page fault. | |||||
| Property | MinimumWorkingSetSize | SeDebugPrivilege | The MinimumWorkingSetSize property indicates the minimum working set size of the process. The working set of a process is the set of memory pages currently visible to the process in physical RAM. These pages are resident and available for an application to use without triggering a page fault. | |||||
| Method | Create | SelncreaseQuotaPrivilege | The Create method creates a new process. | |||||
| Method | Terminate | SeDebugPrivilege | The Terminate method terminates a process and all of its threads. | |||||
| ROOT/CIMV2 | Win32_ComputerSystem | Property | SystemStartupDelay | SeSystemEnvironmentPrivilege | The SystemStartupDelay property indicates the time to delay before starting the operating system
| |||
| Properly | SvstemStartupOptions | SeSystemEnvironmentPrivilege | The SystemStartupOptions property array indicates the options for starting up the computer system. Note that this property is not writable on IA64-btt machines. Constraints: Must have a value.
| |||||
| Property | SvBtemStartupSetting | SeSystemEnvironmentPrivilege | The SystemStartupSetting property indicates the index of the default start profile. This value is 'calculated' so that it usually returns zero (0) because at write-time, the profile string is physically moved to the top of the list. (This is how Windows NT determines which value is the default.)
| |||||
| ROOT/CIMV2 | Win32_OperatingSystem | Method | Reboot | SeShutdownPrivilege | The Reboot method shuts down the computer system, then restarts it. On computers running Windows NT/2000, the calling process must have the SE_SHUTDOWN_NAME privilege. The method returns an integer value that can be interpretted as follows: 0 - Successful completion. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||
| Method | Shutdown | SeShutdownPrivilege | The Shutdown method unloads programs and DLLs to the point where it is safe to turn off the computer. All file buffers are flushed to disk, and all running processes are stopped. On computer systems running Windows NT/2000, the calling process must have the SE_SHUTDOWN_NAME privilege. The method returns an integer value that can be interpretted as follows: 0 - Successful completion. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||||
| Method | Win32Shutdown | SeShutdownPrivilege | The Win32Shutdown method provides the full set of shutdown options supported by Win32 operating systems. The method returns an integer value that can be interpretted as follows: 0 - Successful completion. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||||
| Method | SetDateTime | SeSystemTimePrivilege | The SetDateTime method sets the current system time on the computer. On computer systems running Windows NT/2000, the calling process must have the SE_SYSTEMTIME_NAME privilege. The method returns an integer value that can be interpretted as follows: 0 - Successful completion. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||||
| ROOT/CIMV2 | CIM_LogicalFile | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | CIM_DeviceFile | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | CIM_Directory | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermEsion method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | Win32_Directory | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | CIM_DataFile | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | Win32_ShortcutFile | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | Win32_CodecFile | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| ROOT/CIMV2 | Win32_NTEventlogFile | Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||
| Method | ClearEventlog | SeBackupPrivilege | Clears the specified event log, and optionally saves the current copy of the logfile to a backup file. The method returns an integer value that can be interpretted as follows: 0 - Successful completion. 8 - The user does not have adequate privileges. 21 - Invalid parameter. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||||
| Method | BackupEventlog | SeBackupPrivilege | Saves the specified event log to a backup file. The method returns an integer value that can be interpretted as follows: 0 - Successful completion. 8 - The user does not have adequate privileges. 21 - Invalid parameter. 183 - Archive file name already exists. Cannot create file. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||||
| ROOT/CIMV2 | Win32_PageFile | Class | SeCreatePagefilePrivilege | The Win32_PageFile class has been Deprecated in favor of the Win32_PageFileUsage and Win32_PageFileSetting. These classes respectively correspond to the runtime and persisted states of pagefiles. The Win32_PageFile represents the file used for handling virtual memory file swapping on a Win32 system. Note: The SE_CREATE_PAGEFILE privilege is required for Windows XP and Windows Server 2003. | ||||
| Method | GetEffectivePermission | SeSecurityPrivilege | The GetEffectivePermission method determines whether the caller has the aggregated permissions specified by the Permission argument not only on the file object, but on the share the file or directory resides on (if it is on a share). | |||||
| ROOT/CIMV2 | Win32_NTLogEvent | Class | SeSecurityPrivilege | This class is used to translate instances from the NT Eventlog. | ||||
| ROOT/CIMV2 | Win32_SecuritySetting | Method | GetSecurityDescriptor | SeRestorePrivilege | Retrieves a structural representation of the object's security descriptor | |||
| Method | SetSecurityDescriptor | SeRestorePrivilege | Sets security descriptor to the specified structure | |||||
| ROOT/CIMV2 | Win32_LogicalFileSecuritySetting | Method | GetSecurityDescriptor | SeRestorePrivilege | Retrieves a structural representation of the object's security descriptor. | |||
| Method | SetSecurityDescriptor | SeRestorePrivilege | Sets security descriptor to the specified structure. | |||||
| ROOT/CIMV2 | Win32_LogicalShareSecuritySetting | Method | GetSecurityDescriptor | SeRestorePrivilege | Retrieves a structural representation of the object's security descriptor. The method returns an integer value that can be interpreted as follows: 0 - Successful completion. 2 - The user does not have access to the requested information. 8 - Unknown failure. 9 - The user does not have adequate privileges. 21 - The specified parameter is invalid. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||
| Method | SetSecurityDescriptor | SeRestorePrivilege | Sets security descriptor to the specified structure. The method returns an integer value that can be interpreted as follows: 0 - Successful completion. 2 - The user does not have access to the requested information. 8 - Unknown failure. 9 - The user does not have adequate privileges. 21 - The specified parameter is invalid. Other - For integer values other than those listed above, refer to Win32 error code documentation. | |||||
| ROOT/CIMV2 | Win32_PageFileSetting | Class | SeCreatePagefilePrivilege | The Win32_PageFileSetting class represents the settings of a page file. Information contained within objects instantiated from this class specify the page file parameters used when the file is created at system startup. The properties in this class can be modified and deferred until startup. These settings are different from the run time state of a page file expressed through the associated class Win32_PageFileUsage.
| ||||
| ROOT/CIMV2 | Win32_NTLogEventlog | Class | SeSecurityPrivilege | The Win32_NTLogEventLog class represents an association between an NT log event and the log file that contains the event. | ||||
| ROOT/CIMV2 | CIM_ProcessExecutable | Class | SeDebugPrivilege | A link between a process and a data file indicating that the file participates in the execution of the process.
| ||||
| ROOT/CIMV2 | Win32_NTLogEventUser | Class | SeSecurityPrivilege | The Win32_NTLogEventUser class represents an association between an NT log event and the active user at the time the event was logged. | ||||
| ROOT/CIMV2 | Win32_NTLogEventComputer | Class | SeSecurityPrivilege | The Win32_NTLogEventComputer class represents an association between an NT log event and the computer from which the event was generated. |
4.2.2 The group membership
By default, every CIM repository namespace is secured from the Root namespace, while subnamespaces inherit the security settings from the Root (see Figure 4.1).
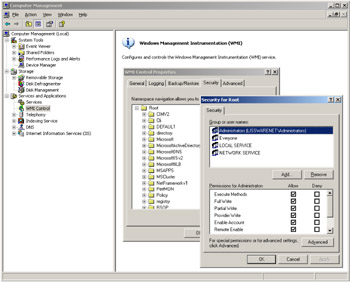
Figure 4.1: The default security settings on the Root namespace.
By default, only two built-in groups are configured to access a CIM repository namespace: Administrators and Everyone. While the Administrators group has full access to any CIM repository namespace by default, the Everyone group is restricted to a limited number of accesses, such as reading some configuration data from the local system.
Table 4.2 summarizes the access type granted to the default groups for the Root namespace. Each of these rights is stored in the CIM repository in the form of a security descriptor.
| Administrators | Everyone | Local Service | Network Service | |
|---|---|---|---|---|
| Execute Methods | X | X | X | X |
| Full Write | X | |||
| Partial Write | X | |||
| Provider Write | X | X | X | X |
| Enable Account | X | X | X | X |
| Remote Enable | X | |||
| Read Security | X | |||
| Edit Security | X |
EAN: 2147483647
Pages: 82