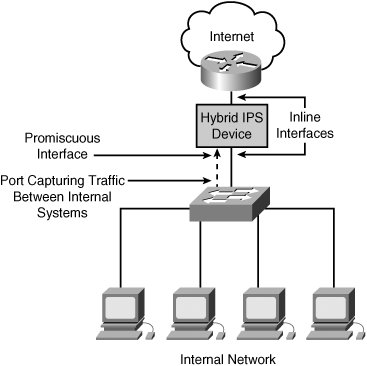
Hybrid IPSIDS Systems
Hybrid IPS/IDS SystemsDeploying separate IDS and IPS devices is cumbersome. Protecting your network using hybrid IPS devices, though, enables you to obtain the benefits of both technologies from a single device because IDS and IPS are complimentary technologies. Using the ongoing network configuration, a hybrid IPS device can provide the IPS protection to prevent an attack coming from or going to the Internet (see Figure7-5). Using IDS functionality, the same device also can watch for attacks going between two internal systems. Figure 7-5. Hybrid IPS Device Providing IPS Protection
|
Intrusion Prevention Fundamentals
ISBN: 1587052393
EAN: 2147483647
EAN: 2147483647
Year: N/A
Pages: 115
Pages: 115
Authors: Earl Carter, Jonathan Hogue