Java Security by Design
| Application security is critical in Java technology. The Java runtime environment (aka JVM) provides a tightly guarded security environment for runtime execution. (Refer to [J2EE14], [J2EE14Tutor], and [LiGong] for more details.) Figure 13-1 depicts a high-level security overview. Inside the JRE, the Security Manager is responsible for code runtime verification and access control. The code runtime verification is managed by the Protection Domain, where different class files (namely, bootstrap class, system class, and user class) are verified by bootstrap class loader, system class loader, class loader, and the bytecode verifier. The Access Module is responsible to authenticate and authorize the principal (user or service requester) against the security policy files (namely, java.security and java.policy files). The JRE supports a variety of authentication mechanisms, including JAAS login module, database security (using JDBC), or LDAP (using JNDI). Figure 13-1. Java security overview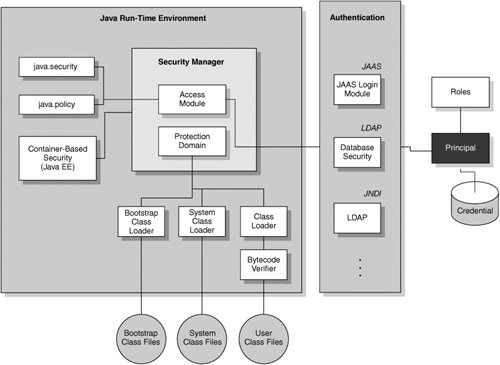 Java Runtime SecurityJava SE provides a Java "sandbox" to restrict applets from accessing file systems and networks and untrusted applets from accessing all of the API functionality. The "sandbox" security architecture (refer to Figure 13-1) consists of three key components:
The security manager has a security policy database where security policies are maintained. The security policy database stores permission rules for authorization and key stores for authentication. A security policy relates to a set of permissions for a domain (system or application), which encloses a set of classes. Developers can also customize any additional protection of resources within the domain boundary, say, using the SignedObject class. The protection domain (java.security.ProtectionDomain class) is another important security concept. It refers to the system and application components (for example, a group of classes) of the runtime environment that can be secured according to the predefined security policy. There are two types of protection domain: static (grant permissions specified only when constructed) and dynamic (grant permissions specified when constructed and permissions granted by the security policy). The protection domain extends the "sandbox" security architecture by associating a group of principals with permissions. For example, a protection domain associates permissions with a code source (URL where the class file comes from), such that any classes originating from the same URL will have the same signature and key placed in the same domain, and thus granted the same permissions and access rights. This enhances the current mechanism to load a class. Moreover, the security policy allows defining an association between the principals and permissions for the classes (via the code source). It can be passed as a parameter to the application, which can use different protection domains wherever necessary. Java SE security introduces a set of additional security concepts (see [LiGong] for details), which includes the concepts of a Principal (an entity that a security service can authenticate with an authentication protocol) and security domain (the scope related to a set of security policies defined by the administrator of a security service). There are two important files under JVM that store security policy information: java.policy and java.security under the directory, %J2SE%/lib/security, where %J2SE% is the file location for the JVM. Authentication MechanismsFigure 13-1 shows an example of three different authentication mechanisms. A subject (user) has multiple principals, or multiple user names or identities. Suppose one of his principals (using the java.security.Principal class) possesses a digital certificate as a credential. Under the Java SE security architecture, the principal can use the credential to authenticate with the applications via JAAS (using the javax.security.auth.login.* class), JNDI (using the LDAP directory server), or JDBC (using back-end database security). In this example, the security manager is used. Upon successful authentication, the security manager will check permission, and pass control to the access module. The access module (using the java.security.AccessController class) checks permission by checking the java.security file, which contains the policy URL (policy.url.1) and keystore information (keystore.type). The java.security file associates the permission (grant ... permission ...) with the principals. If the principal-permission relationship is found, then the access module grants access to the principal for the application resources to the principal. Apart from the "sandbox" security architecture, Java SE also provides some authentication and encryption services that work with JCA and JCE layers. These security services include JAAS, JSSE, JGSS, and CertPath. Applications or security packages can also customize their security APIs using these security services. Container-Based SecurityThe Java EE container provides a comprehensive application-level security that is related to the application component deployment and runtime environment.
Security Interoperability FeaturesJava technology has provided several interoperability features to secure business applications. The following highlights a few major security interoperability features:
|
EAN: 2147483647
Pages: 170