Using NTFS
There are two ways of protecting the files on your Windows XP/Windows 2003 system. You have already seen security applied at the share level, and now you will look at a second method: NTFS security. The basic differences between these are:
| Share | NTFS |
|---|---|
| In effect regardless of where the user connects to the resource | Only takes effect if the user accesses the resource using the share |
| Permissions include Full Control, Read, and Deny | Has more complex permissions, including Read Write, List Folder Contents, Read and Execute, Modify, and Full Control |
| Security on files and folders | Security only at the folder level |
NTFS is more than just a security system, though. It is a file system that offers enhancements over the traditional FAT system used by Microsoft DOS and Windows. It is also significantly different from the FAT32 system utilized by Windows 95/98. This section will examine what NTFS is, and the services and options it gives you when configuring your system.
| Note | FAT32 support was new to Windows 2000. Windows NT 4 computers support only FAT16 and NTFS. |
To determine the type of file system that is installed on an existing Windows XP/Server 2003 drive, right-click the drive in the Explorer and select Properties. Information will be presented about the drive, including its file system and size.

Selecting a File System
Each local drive on a Windows server must be formatted with a file system before it can be used to store data. A file system defines how information is stored on the disk and defines the properties that can be applied to files. Windows servers support four file systems:
-
FAT (File Allocation Table)
-
FAT32 (File Allocation Table, 32 bit edition)
-
NTFS (New Technology File System)
-
CDFS (Compact Disc File System)
Computer Management utility
Used to monitor and configure the Windows2000 Server and Windows Server 2003 computer. System tools, system drives, and services can all be configured from here.
When you format your disk partition, you use FAT/FAT32 or NTFS. This table describes some of the major differences between them.
| FAT/FAT32 | NTFS |
|---|---|
| Operating systems such as DOS, OS/2, Windows 3.x, Windows 95/98/Me, Windows 2000/XP Server and Windows Server 2003 all support FAT. If you require dual-boot capability to one of these other operating systems, you must use FAT. | Windows NT, 2000 and XP, and Windows Server 2003 are the only operating systems that can access an NTFS partition. If your computer uses only 2000/XP Server or Windows Server 2003, this partition type will be accessible, but if you wish to dual-boot to DOS or Windows 95/98/Me, you must use FAT. |
| Windows 95/98/Me and Windows 2000, Windows XP, and Windows Server 2003 support FAT32. If you require dual-boot capability to Win95/98/Me, you may choose to use FAT32. | |
| FAT/FAT32 offers no local security. This means that if multiple users share the same computer, all data stored on the FAT partition is available to all users. | One of the main advantages of NTFS is that you can specify local security. Because logon is mandatory, you can specify what rights users and groups have to NTFS folders and files. |
| No native file compression or encryption is available. | File compression and encryption is supported, although you can only use either file compression or encryption on a folder, not both at the same time. |
| No support is available for Macintosh files. | You can store and share Macintosh files on NTFS partitions. |
| You can convert FAT/FAT32 to NTFS at any time (except the partition with the system files, the actual conversion will take place during the next restart). | The only way you can go from NTFS back to FAT is to reformat your partition. This means that you will lose all data, and you must restore it from backup. |
Understanding the Basics of NTFS
NTFS is the native file system of the Windows 2000/XP Server and Windows Server 2003 operating systems. You can format a disk partition to use NTFS through the 2000/XP Server or Windows Server 2003 installation or with the Computer Management utility. To convert an existing FAT disk partition to NTFS, you use the CONVERT command-line utility as seen here:
CONVERT [drive letter]: /fs:NTFS
For example, if you want to convert the C drive, you use this syntax:
CONVERT C: /fs:NTFS
local security
Permissions settings that take effect even if the user is working locally on the machine where the resource is located.
The main advantage of the NTFS file system is that you can apply local security, also referred to as local permissions. For example, assume that you have two users, Terry and Ron, who share the same computer. Each user has a folder at the root of C:\ called TERRY and RON, respectively. With NTFS permissions, you can specify that only user Terry has permission to the TERRY folder and only user Ron has permission to the RON folder. This is possible only with NTFS and cannot be defined on FAT partitions.
When you format a partition as NTFS, permissions are applied in two ways:
-
To any user who accesses the computer locally, meaning that user is logged on to the computer where the resource is located
-
To any user who accesses an NTFS folder that has been shared over the network
| Note | NTFS permissions are different from share permissions in that you can apply them to folders and files. |
| Warning | As with shared folders, the default NTFS permissions for any newly created NTFS drive is that the group Everyone has Full Control. |
Assigning NTFS Permissions
NTFS permissions allow for far more specific permission assignments than share permissions.
NTFS permissions can be set at two levels: the file level and the folder level. As you have seen, share permissions are set only on folders.
Folder level Setting a permission at the folder level changes the attribute for the folder object, and also changes the default permissions of any new files or subfolders created in the folder. Existing files in the folder may also be set to the new permissions. Folder-level permissions include the following:
| Permission | Allows |
|---|---|
| Read | View folder and files within it. |
| Write | Create new files and subfolders. |
| List Folder Contents | See the contents of the folder. |
| Read and Execute | View and run programs from the directory. |
| Modify | Change properties or delete the folder. |
| Full Control | Change permissions and ownership. Can create, modify, or delete folder and files. |
File level Permissions set at the file level are generally best left the same as the folder they reside within, but this does not have to be the case. Each file has the capability to support security on its own. The following permissions can be set at the file level:
| Permission | Allows |
|---|---|
| Read | View the file and its attributes. |
| Write | Change the content of the file. |
| Read and Execute | Used on a program file, it allows the user to run the program. |
| Modify | Includes Read as well as Read and Execute, but also allows the file to be deleted. |
| Full Control | Change permissions and ownership. Can modify or delete the file. |
You apply NTFS permissions in a similar fashion to share permissions. One difference is that you apply share permissions to folders, and you apply NTFS permissions to folders and files.
Combining NTFS and Share Permissions
NTFS is similar to share permissions in the sense that if a user belongs to multiple groups that have been granted access to the same resource, the least restrictive access permission is applied. The exception to this rule is if the Deny permission has been specified. A user given Deny through any user assignment or group membership has no access to the specified resource.
If a user has a different set of permissions for a folder and the files within the folder, the file permissions are applied.
As an example, assume this directory structure:
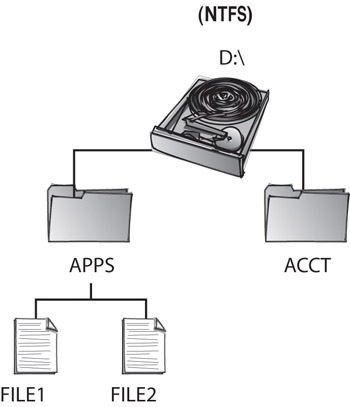
These assignments have been made:
| Resource | Assignment | Permission |
|---|---|---|
| D:\APPS | Everyone | Read |
| D:\APPS\FILE2 | Everyone | Modify |
| D:\ACCT | Temps | Deny Read, Deny Modify |
| Accountants | Modify | |
| Managers | Full Control |
These assignments mean:
-
When accessing the D:\APPS folder locally, all users have Read permissions to the files in the folder except for FILE2, which has been explicitly assigned a different permission.
-
A user belonging to Temps and Accountants would still have no local access to D:\ACCT, because Deny overwrites any other permission assignments.
Applying NTFS Permissions
To implement NTFS permissions, you must first format the disk partition as NTFS. If you have an existing partition, you use the CONVERT command to save existing data.
To access the Directory Permissions dialog box, which you use to assign NTFS security, complete these steps:
-
From Windows Explorer, single-click the folder you want to apply permissions on.
-
Right-click the folder and select Sharing And Security.
-
Select the Security tab to view the Permissions area, shown here:

-
You will notice that the group Everyone has Full Control permission by default. To remove this assignment, highlight Everyone and click the Remove button.
-
To make a new assignment, click the Add button to see the Select Users, Computers, or Groups dialog box.
-
For each group you want to assign permissions to, highlight the group in the Name box and click the Add button. Click the OK button.
-
Back at the main permissions window, select each group and set the permissions they need.
Note To manipulate NTFS permissions, you must be logged on as a user with Full Control to the folder whose permissions you want to manipulate.
|
|