Spooler Subsystem
The HP NonStop server SpoolerPlus Subsystem is a set of utilities that presents an interface between users and applications and the print devices of a system. The Spooler receives output from applications and stores it on disk. This output can be a report in EDIT format, a compiled listing, or any other data. The data stays on disk and can reviewed before printing. If directed to a print location, when the designated print device becomes available, the output is printed.
RISK Printed output is an important way that data is reported . It may also provide unwanted access to sensitive data and can be easily distributed to non- authorized personnel.
AP-ADVICE-SPOOLER-01 The Corporate Security Policy should detail procedures for the physical security of printers and printer output.
Spooler Subsystem Components
The Spooler is made up of the following components (See Figure 6-9):
Collectors
FONT Utility
PERUSE
Print Processes
RP Setup Utility
SPOOLCOM
Supervisors
Spooler Data Files
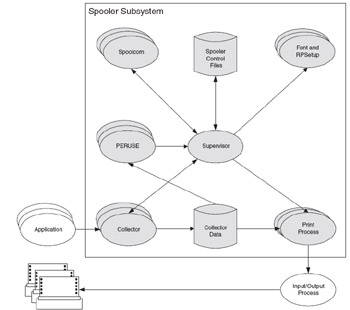
Figure 6.9: SPOOLER Subsystem Components
Collectors
Collector processes accept output from applications and store it on disk. There can be up to 15 collectors associated with a given Spooler. Collectors are run in non-stop pairs. The spooler collector object file is $SYSTEM.SYSTEM.CSPOOL. The typical default collector process name is $S.
Applications direct output to a collector by treating the collector as an OUT file.
TGAL / IN <file>, OUT $S /
An application can open a file to any collector and begin writing its output using the Guardian file system WRITE[X] procedure. Applications can also use the spooler interface procedures to spool their output .
FONT
The FONT utility is used to create FONT jobs. Font job descriptions are created in an EDIT file, called a script file, and then the Font utility is used to configure the selected spooler locations with the indicated font jobs.
Script Files contain commands that can be sent to a printer to control such features as character sets, vertical forms-control specifications, or compressed printing. Such files frequently contain both printable and nonprintable text, but the Font utility makes it possible to enter all font descriptions in plain text; no nonprintable characters are used.
PERUSE
PERUSE is an interactive program that enables users to examine jobs and their attributes while in the spooler subsystem. With PERUSE it is possible to:
View job contents
Display a job while it is being spooled
Monitor changes in job status
Alter job attributes
Redirect jobs to a print location
Copy a job from the spooler queue to an EDIT file or a spooler job file
Copy a spooler job file to the spooler queue
Link/unlink jobs to batches
The internal PERUSE security is as follows :
Users can view and manipulate only their own jobs.
The job creator can always access the job.
A Group Manager can view or manipulate all jobs belonging to that manager's group members .
SUPER Group members can view and manipulate all jobs, regardless of ownership.
RISK Any user with PERUSE access to a job has access to the job output's contents.
PERUSE Commands with Security Implications
This section describes only the PERUSE commands which pose security risks.
BATCH
DEV
FORM
JOB
LINK
LIST*
LOC
OPEN
PURGE
REPORT
UNLINK
RISK The LIST command displays or prints the job output. If the output contains sensitive data, that data is at risk of exposure.
If a third party access control product is used to grant selected users access to PERUSE running as a SUPER Group member or another privileged userid (such as the userid that owns application jobs), access to the sensitive commands should only be granted to the appropriate users and denied to all others.
Print Processes
Print processes retrieve the output stored on disk by a collector and print it to a device. There are multiple print processes. Each print device in the Spooler Subsystem has a print process associated with it.
FASTP
FASTP is the print process that ships with the Spooler. The FASTP print process uses a configuration file named FASTCNFG.
RISK A FASTCNFG file usually contains information that should not be accessible to all users.
AP-ADVICE-SPOOLER-02 FASTCNFG must be secured for READ access by the FASTP print process only.
RPSETUP Utility
The RPSetup utility configures cross-spooler connections between spoolers in a network allowing users access to printers on remote nodes. The utility makes it possible for print jobs from local applications to be sent to a remote spooler and queued for printing on remote printers.
RISK Allowing print jobs to be networked may reduce the amount of physical security over the printed materials.
SPOOLCOM
SPOOLCOM is the command interpreter for the Spooler Subsystem. It is used to:
Display the status of collectors.
Display the status of devices.
Display the status of jobs.
Display the status of print processes.
Display the status of the routing structure.
Display the status of the spooler itself.
Change the location, state or any other attribute of a job.
Delete jobs.
Restart devices that have gone offline because of device errors.
SPOOLCOM Commands with Security Implications
This section describes only the SPOOLCOM commands that pose security risks.
BATCH*
COLLECT
DEV*
FONT
JOB*
LOC
OPEN
SPOOLER
The commands marked with an asterisk (*) can be used by job owners to alter their own jobs. Members of the SUPER Group can modify any user's jobs.
All users can use the STATUS subcommand to obtain information about Collectors, Devices, Font Jobs, Locations, Printers and Spooler Supervisors, but only members of the SUPER Group can alter the configuration of any of these items.
Any SUPER Group member is allowed to manipulate any jobs and devices.
If a third party access control product is used to grant selected users access to SPOOLCOM only the commands listed above should be granted to general users. All other commands should be restricted.
3P-ACCESS-SPOOLER-01 Use a third party access control product to allow the users responsible for maintaining the Spooler subsystem access to the sensitive commands.
3P-PROCESS-SPOOLER-01 Use a third party access print job manager product that allows for global management of jobs.
3P-PROCESS-SPOOLER-02 Use a third party product that allows a designated user to manage jobs without ownership and without the ability to view the data in the job.
Without a third party access control product:
AP-ADVICE-SPOOLER-01 Spooler processes should run as a job function userid, such as SUPER.SPOOLER, which is not assigned to any individual.
Supervisors
The Spooler Supervisor monitors and communicates with the other programs and determines when and where to print jobs. There is only one Supervisor in each spooler subsystem; but there can be more than one Spooler Subsystem operating at a time.
The spooler object file is $SYSTEM.SYSTEM.SPOOL. The typical default process name is $SPLS.
Spooler Data Files
When a spooler subsystem is configured, an associated datafile is created to store the output on disk until printed or deleted. This file may be located on any disk volume and will be pre-created at its fully allocated size . The default data file name is SPLDATA.
BP-SPOOLER-CONFIG-01 The spooler data file should not be located on $SYSTEM to avoid contention . Configure the data file on another, less busy, volume.
Securing Spooler Components
BP-PROCESS-CSPOOL-01 $S process should be running.
BP-FILE-SPOOLER “01 CSPOOL should be secured "UUNU".
BP-OPSYS-OWNER-02 CSPOOL should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 CSPOOL must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “02 FASTCNFG should be secured "NUUU".
BP-OPSYS-OWNER-02 FASTCNFG should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 FASTCNFG must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “03 FASTP should be secured "UUNU".
BP-OPSYS-OWNER-02 FASTP should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 FASTP must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “04 FONT should be secured "UUNU".
BP-OPSYS-OWNER-02 FONT should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 FONT must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “05 PERUSE should be secured "UUNU".
BP-OPSYS-OWNER-02 PERUSE should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 PERUSE must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “06 PSPOOL / PSPOOLB should be secured "UUNU".
BP-OPSYS-OWNER-02 PSPOOL / PSPOOLB should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 PSPOOL / PSPOOLB must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “07 RPSETUP should be secured "UUCU".
BP-OPSYS-OWNER-02 RPSETUP should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 RPSETUP must reside in $SYSTEM.SYSTEM
BP-PROCESS-SPOOL-01 $SPLS process should be running.
BP-FILE-SPOOLER-08 SPOOL should be secured "UUNU".
BP-OPSYS-OWNER-02 SPOOL should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 SPOOL must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “09 SPOOLCOM should be secured "UUNU".
BP-OPSYS-OWNER-02 SPOOLCOM should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 SPOOLCOM must reside in $SYSTEM.SYSTEM
BP-PROCESS-SPOOLPA-01 $SPLP process should be running.
BP-FILE-SPOOLER “10 SPOOLP/SPOOLPA should be secured "UUNU".
BP-OPSYS-OWNER-02 SPOOLP/SPOOLPA should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-02 SPOOLCOM must reside in $SYSTEM.SYSTEM
BP-FILE-SPOOLER “11 SPLDATA should be secured "NUUU".
BP-OPSYS-OWNER-03 SPLDATA should be owned by SUPER.SUPER.
BP-OPSYS-FILELOC-03 SPLDATA resides in $SYSTEM.??
If available, use Safeguard software or a third party object security product to grant access to the SPOOLER object files only to users who require it in order to perform their jobs.
BP-SAFE-SPOOLER-01 Add a Safeguard Protection Record to grant appropriate access to the FASTP object file.
BP-SAFE-SPOOLER-02 Add a Safeguard Protection Record to grant appropriate access to the RPSETUP object file.
BP-SAFE-SPOOLER-03 Add a Safeguard Protection Record to grant appropriate access to the SPOOLCOM object file.
Many corporations are faced with a printing dilemma: there are multiple applications, each producing jobs with spooled output and each with a unique application ownerid, but the operators must manage ALL the jobs, regardless of ownership.
With a third party access control product or print control process:
3P-ACCESS-SPOOLER-03 Use a third party access control product to allow the users responsible for producing jobs with spooled output the ability to run SPOOLCOM as SUPER.SUPER.
3P-OBJSEC-SPOOLER-04 Use a third party access print job manager product that allows for global management of jobs.
Without a third party access control product:
AP-ADVICE-SPOOLER-03 Give operators a userids in the SUPER Group or give aliases to a SUPER Group member.
RISK SUPER Group members have many inherent privileges that the Operators should not have.
AP-ADVICE-SPOOLER-04 Give those users responsible for managing print jobs EXECUTE access to a PROGID'd copy of the SPOOLCOM and PERUSE utility owned by SUPER.SUPER.
RISK Object files PROGID'd to SUPER.SUPER are a security risk.
AP-ADVICE-SPOOLER-04A The PROGID'd copies of SPOOLCOM and PERUSE should be secured so that only users authorized for this function can execute them.
| Discovery Questions | Look here: | |
|---|---|---|
| FILE-POLICY | What is the corporate policy on managing print functions | Policy |
| PROCESS-CSPOOL-01 | Is the $S process running? | Status |
| PROCESS-SPOOL-01 | Is the $SPLS process running? | Status |
| PROCESS-SPOOLPA-01 | Is the $SPLP process running? | Status |
| OPSYS-OWNER-02 | Who owns the CSPOOL object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the FASTCNFG object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the FASTP object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the FONT object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the PERUSE object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the PSPOOL/PSPOOLB object files? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the RPSETUP object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the SPOOL object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the SPOOLCOM object file? | Fileinfo |
| OPSYS-OWNER-02 | Who owns the SPOOLP/SPOOLPA object files? | Fileinfo |
| OPSYS-OWNER-03 | Who owns the SPLDATA object file? | Fileinfo |
| FILE-POLICY | Who is allowed to manage the SPOOLER subsystem on the system? | Policy |
| FILE-SPOOLER-01 | Is the CSPOOL object file secured correctly? | Fileinfo |
| FILE-SPOOLER-02 | Is the FASTCNFG file correctly secured? | Fileinfo |
| FILE-SPOOLER-03 SAFE-SPOOLER-01 | Is the FASTP object file correctly secured with the Guardian or Safeguard system? | Fileinfo Safecom |
| FILE-SPOOLER-04 | Is the FONT object file correctly secured ? | Fileinfo |
| FILE-SPOOLER-05 | Is the PERUSE object file correctly secured? | Fileinfo |
| FILE-SPOOLER-06 | Is the PSPOOL/PSPOOLB object files correctly secured? | Fileinfo |
| FILE-SPOOLER-07 SAFE-SPOOLER-02 | Is the RPSETUP object file correctly secured with the Guardian or Safeguard system? | Fileinfo Safecom |
| FILE-SPOOLER-08 | Is the SPOOL object file correctly secured with the Guardian or Safeguard system? | Fileinfo |
| FILE-SPOOLER-09 SAFE-SPOOLER-03 | Is the SPOOLCOM object file correctly secured with the Guardian or Safeguard system? | Fileinfo Safecom |
| FILE-SPOOLER-10 | Is the SPOOLP/SPOOLPA object files correctly secured? Fileinfo | |
| FILE-SPOOLER-11 | Are the SPLDATA data files correctly secured? | Fileinfo |