A globally unique identifier for an object’s class in Active Directory. An object identifier for an attribute remains unchanged even when the distinguished name of the object is modified because of system configuration changes. Object identifiers ensure that when Active Directory is integrated with other directory systems such as Novell Directory Services (NDS), X.500, or Simple Network Management Protocol (SNMP), no conflicts occur between them. Each class of object in Active Directory has a unique object identifier that is externally assigned by an issuing authority. In the United States, the issuing authority is the American National Standards Institute (ANSI). The International Organization for Standardization (ISO) maintains a list of the world’s issuing authorities. An object’s attributes also require unique object identifiers.
TIP
If you want to create new classes of objects or new attributes in Active Directory using Active Directory Schema Manager, you must obtain an object identifier for your organization. An example of an object identifier for a U.S. company is 1.2.840.105670, where 1.2.840 is assigned to U.S. companies and 105670 is the number assigned to the specific company. Once your company has an object identifier, you can extend it by appending dotted decimal portions. So if 1.2.840.105670 represents Northwind Traders, 1.2.840.105670.27 might represent the Sales division, 1.2.840.105670.33 might represent the Support division, and so on. Further levels of subdivision are also possible.
The basic element of Active Directory in Microsoft Windows 2000 that represents something on the network, such as a user, a group, a computer, an application, a printer, or a shared folder.
How It Works
Objects have attributes that define and describe them. For example, the attributes of a user object might include the user’s name, e-mail address, and phone number. All objects of the same type or class have the same set of attributes, but they are distinguished from each other by having different values for at least one of these attributes. Some attributes are required to have values (such as the First Name attribute of a user object), while other attributes can be optional (such as Telephone Number).
You can group objects by placing them into container objects (containers) such as the ones following:
Domains: The fundamental units of Active Directory that share common administration, security, and replication requirements. Domains can also be grouped into domain trees and forests to reflect the administrative structure of an enterprise.
Organizational units (OUs): Container objects that are used to organize other directory objects. OUs make possible the hierarchical structure of Active Directory, in which objects are grouped according to common functions and purposes to simplify network administration. The hierarchical grouping of objects and OUs also simplifies the process of searching Active Directory for information about network resources.
Access to an object in Active Directory is based on the object’s discretionary access control lists (DACLs), which list the users and groups authorized to access the object and their access levels. You can group objects with similar security requirements into OUs to simplify assignment of permissions to the objects and to facilitate administration and control of network resources. You can assign permissions to objects by using Active Directory Users and Computers, a snap-in for Microsoft Management Console (MMC).
Objects can be referenced by name by using
Distinguished names: Analogous to absolute paths of objects within a file system. The distinguished name of an object specifies complete information about the object’s location within Active Directory and includes the domain name, names of OUs that it belongs to, and the name of the object itself. Each object in Active Directory must have a unique distinguished name.
Relative distinguished names: Analogous to relative paths of objects in the current directory of a file system. The relative distinguished name of an object is the portion of the distinguished name that is unique to the object. Any two objects in the same OU must have unique, differing relative distinguished names.
The most common types of objects in Active Directory are as follows:
User account objects: Required for users to log on to the network.
Group objects: Collections of user accounts, computers, or other groups created for organizational purposes or for assigning permissions to shared resources.
Computers: Represent machines that belong to the domain.
Shared folders: Pointers to shared folders on a server on the network. If you create a shared folder on a computer running Windows 2000, an associated shared folder object is automatically created in Active Directory.
Printers: Pointers to printers on the network. If you create a network printer on a machine running Windows 2000, an associated printer object is automatically created in Active Directory.
OUs: Containers for organizing other objects in a hierarchical fashion.
TIP
When you use Active Directory Users and Computers to view the property sheet for an object, the Security tab, which displays the Active Directory permissions assigned to that object, is usually not visible. Choose Advanced Features from the View menu to make this tab visible.
TIP
If you have resources such as shared folders or printers on computers that are not running Windows 2000, you must manually publish information about these resources in Active Directory if you want users to be able to locate and access them through Active Directory. You do this by adding the appropriate type of object for that resource to Active Directory and having it point to where the resource is located on the network.
TIP
When you create a new Active Directory object, you usually use a wizard to specify values for the important attributes of the object. You can specify other attributes after the object is created by opening the property sheet for that object.
A construct containing data as well as methods (functions for manipulating the construct’s data). Object-oriented programming (OOP) focuses on objects instead of functions for manipulating separate data entities. The “blueprint” for an object is a class; a specific object is an “instance” of a class that you access using its associated methods. New classes can be derived from more general classes through a procedure called inheritance. The derived class contains all the methods and data of the original class, which can simplify programming.
A component or aspect of a server for which you can collect and analyze usage statistics. Examples of objects in the Microsoft Windows NT and Windows 2000 administrative tool Performance Monitor include caches, logical disks, memory, processors, and threads. When an object is monitored, data is collected for every instance of every counter for the object.
See also Performance Monitor
A system resource that can be made available to an application. Examples of objects in Microsoft Windows NT and Windows 2000 include files, printers, memory, devices, windows, threads, and processes. A file object, for example, includes the file’s name and status information, along with a collection of methods for creating, opening, closing, and deleting the object. These methods describe what actions can be performed on the object by the Object Manager, the component of the Windows NT executive that manages resources on a machine running Windows NT or Windows 2000.
A feature that allows users to create and edit documents that contain objects created by different applications. For example, you can embed bitmap images, sound clips, spreadsheet files, and other objects in Microsoft Word documents.
The term “object linking and embedding” comes from these two types of actions for creating compound documents:
Linking adds a link in a document that points to source data stored somewhere else. Linked objects are stored in the document as a path to the original linked data, usually a separate file from the container document.
Embedding, on the other hand, adds one document directly to the other. Embedded objects are stored with the document that contains them.
See also OLE
A component of Windows NT executive running in kernel mode that creates, deletes, and manages executive objects (data types that represent system resources) and manages the global namespace for the Microsoft Windows NT and Windows 2000 operating systems.
How It Works
Windows NT and Windows 2000 are considered object-based operating systems because they control access to all system objects (system resources such as files, printers, and threads). Applications running on Windows NT or Windows 2000 cannot manipulate system resources directly—they must ask Windows NT or Windows 2000 to perform the desired action on the object. This feature provides the basis for all Windows NT and Windows 2000 security, including access control, auditing, and memory protection.
All operating system resources in Windows NT and Windows 2000 are implemented as objects, which are abstract representations of the resources that the operating system can manage. The Object Manager performs actions such as creating, monitoring, and securing the object by invoking the object’s methods. The Object Manager also maintains a global hierarchical namespace of all the objects managed by Windows NT and Windows 2000.
See out-of-band management (OBM)
See optical carrier (OC-x) levels
See open database connectivity (ODBC)
A feature of Internet Information Services (IIS) that allows logs of Web site activity to be written directly to a database that is compliant with the open database connectivity (ODBC) protocol. You can analyze the record of Web site traffic stored in the database and generate reports using standard database analysis tools. This is more convenient than logging Web traffic in text files and then importing them into database tables.
TIP
The Usage Import utility of Microsoft Site Server Express supports only the IIS and NCSA log file formats, so if you want to use Usage Import and Report Writer to generate reports of your Web site traffic, don’t use ODBC logging to collect the information—use Microsoft IIS Log File Format or NCSA Common Log File Format instead.
See Open Data-link Interface (ODI)
A feature of Microsoft Internet Explorer that allows users to browse cached or subscribed Web content when they are not connected to the Internet. Offline browsing is an easy way to browse Web content on a laptop when an Internet connection is not available. Users can surf their history folder to view recently accessed Uniform Resource Locators (URLs). If users click on an unsaved link, they are notified that they are working offline and are asked whether they would like to connect to the Internet to access the resource.
TIP
When you add a Web page to your Favorites list, you can specify that the page be available for offline browsing, indicate how deep you want to be able to browse the page’s links offline, and specify how you want to keep the offline content up to date. To view the site offline later, you can
Choose Synchronize from the Favorites menu to manually synchronize offline content
Choose Work Offline from the File menu to switch to offline browsing mode
Select the item from your Favorites list
To leave Work Offline mode, choose Work Offline from the File menu.
A feature that lets you continue working with shared network resources after you disconnect from the network. Shared files and folders from any computer that supports SMB-based file and print sharing (such as Microsoft Windows 2000, Windows NT 4, Windows 98, and Windows 95) can be made available for offline use by Windows 2000 clients. Windows 2000 clients that are configured to use offline folders can cache the network resources in a local folder. When disconnected from the network, the client can continue working normally on the cached files. The client can then synchronize the contents of the cache with the network share when the connection is restored.
How It Works
To enable offline file support on a computer running Windows 2000, open My Computer and choose Folder Options from the Tools menu. Select the Offline Files tab and check Enable Offline Files.
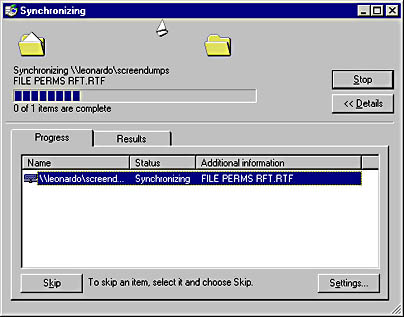
Specify synchronization options, a cache size, and additional advanced options. To make a share on the network available for offline use, select the share in My Computer (where it might appear as a mapped network drive) or My Network Places (where it will appear as a network share) and choose Make Available Offline from the File menu. The contents of the network share will be copied to the local computer’s cache in a process known as synchronizing. You can specify additional synchronization settings by selecting Settings in the Synchronizing dialog box.
Graphic O-1. Synchronizing with a network share using Offline Files in Windows 2000.
A feature that allows users to copy the contents of server-based folders to their hard disks or to a network share. Offline folders have a format similar to personal folders, but they have the extension .ost instead of .pst. To copy information to offline folders, you choose Synchronize from the Tools menu on the Outlook toolbar and select the synchronization method that you want to use.
NOTE
In Microsoft Outlook, the following folders are always considered as a group; if one of them is marked for offline use, all of them are:
Inbox
Outbox
Deleted Items
Sent Items
Contacts
Journal
Notes
Tasks
See online analytical processing (OLAP)
A low-level object-oriented technology based on the Component Object Model (COM) that provides services to applications for creating compound documents.
How It Works
An OLE application can be one or both of the following:
An OLE server application, which is used to create objects that will be contained in compound documents. A server application can create OLE components that can be placed in documents created by OLE container applications.
An OLE container application, which is used to create the actual compound documents. A container application can create documents that can contain and display OLE components using OLE.
OLE container documents support in-place activation, which allows users to activate an embedded OLE component from within the container document. Activating the component changes the container application’s user interface to include features that allow users to directly edit the component from within the container document.
NOTE
The meaning of the term “OLE” has changed since its first usage at Microsoft. Version 1 of Object Linking and Embedding (OLE), referred to as OLE 1, was created in 1991 and was Microsoft’s first mechanism for creating compound documents. OLE 2, the second version of OLE, improved on OLE 1 and expanded the support for creating compound documents. OLE 2 was based on the model known as the Component Object Model (COM). Microsoft began to recognize that OLE 2 could be used to solve other software problems and that it could be applied to other areas of software development. Microsoft saw OLE 2 as an expandable architecture to create software and, as such, decided to drop the version number. Microsoft also reduced the name from “Object Linking and Embedding (OLE)” to just “OLE,” which had no spell-out. At that time, OLE referred to any technology based on COM. In 1996, Microsoft introduced the name “ActiveX.” Initially, the name “ActiveX” referred to COM-based technologies related to the Internet, which overlapped with OLE. Soon, OLE technologies were being referred to as “ActiveX technologies.” At that time, Microsoft decided to change the name “OLE” back to its original name, “object linking and embedding (OLE),” and once again use it to refer to technologies for creating compound documents and the linking and embedding of objects.
See also ActiveX, Component Object Model (COM), object linking and embedding (OLE)
A set of open, extensible interfaces developed by Microsoft and based on OLE/COM technologies for providing applications with uniform methods of data access in diverse data sources. These data sources can include mainframe databases such as IBM’s Information Management System (IMS) and DB2; server databases such as Microsoft SQL Server and Oracle; desktop databases such as Microsoft Access, Microsoft FoxPro, and Paradox; and non-DBMS information sources such as file systems, spreadsheets, text files, and e-mail. OLE DB defines interfaces that encapsulate various types of database functionality such as record containers, query processors, and transaction coordinators. OLE DB facilitates the development of applications that combine various types of database queries from diverse sources.
How It Works
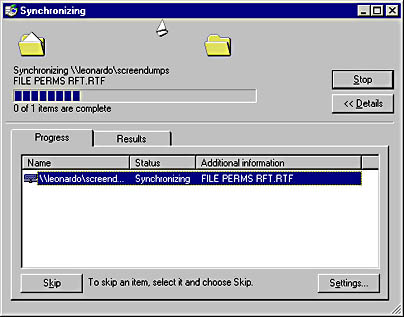
The architecture of an OLE DB system has three parts:
Data source: Can be any ODBC-compliant database, a legacy mainframe system, or another common data source.
OLE DB consumer: Represents the traditional client that needs to access data from the data source.
OLE DB provider: A set of COM components that extracts the requested data from the data source and returns it in tabular format to the OLE DB consumer. The type of provider you use depends on the type of data source the client needs to access. Providers are available for the full range of data sources including ODBC, SQL Server, Jet, Oracle, and AS/400.
Because of the standard set of interfaces used in OLE DB providers, any consumer is able to access data from any provider. Furthermore, because providers are COM objects, consumers can access them using any programming language, including C++, Microsoft Visual Basic, and Java.
Graphic O-2. The architecture of an OLE DB system.
As an example of a provider, the OLE DB Provider for AS/400 and VSAM enables record-level access to mainframe Virtual Storage Access Method (VSAM) files and to the AS/400 native file system. The OLE DB Provider for AS/400 and VSAM is included with Microsoft SNA Server version 4. You use the OLE DB Provider for AS/400 and VSAM to develop applications for discrete data access and for record-level access to physical and logical files on AS/400 systems, in Partitioned Data Sets (PDS’s) and Partitioned Data Set Extended (PDSE) files, and in most versions of VSAM on mainframes. Using the OLE DB Provider for AS/400 and VSAM, programmers can access mainframe VSAM or AS/400 data using Microsoft’s object-based OLE DB data access technology. Programmers can thus access source data from host systems without having to learn about Systems Network Architecture (SNA) or host applications programming. The OLE DB Provider for AS/400 and VSAM facilitates a broad range of data access, from individual records to complete files. Using ActiveX Data Objects (ADO), you can develop web-to-host integration solutions using programming languages such as Microsoft Visual Basic or scripting languages such as Microsoft Visual Basic, Scripting Edition (VBScript), and Microsoft JScript.
A set of Component Object Model (COM) interfaces and objects that extends OLE DB to allow access to information stored in multidimensional information sources. OLE DB for OLAP is included in OLE DB 2.0 and leverages the OLE DB architecture to enable online analytical processing (OLAP) functions for COM-based applications.
A technology that allows users to perform sophisticated data analysis on typically large amounts of enterprise data to gain insight on the information it contains. Examples of analysis include financial modeling, budget forecasting, production planning, and determining broad sales and distribution trends. A query issued in an online analytical processing (OLAP) system could be, “What would be the effect on sales over the next three quarters if the cost of widgets went up 5% while sales dropped 15%?” OLAP systems primarily focus on queries that ask “What if…?” In other words, OLAP systems are designed for making predictions, modeling scenarios, and supporting decision-making.
The database for an OLAP system is structured to allow for efficient retrieval of information. The database can be a data warehouse. A data warehouse is a database that contains static data on a particular subject, drawn from various sources. Queries issued against data warehouses tend to focus on queries that ask “What was…?” or “Who did…?” and are useful for analyzing past sales and growth figures. For example, “What were the total sales for the five largest subsidiaries in the first two quarters of last year?” OLAP systems and data warehouses thus constitute two complementary tools for analyzing and interpreting business data in order to make smart decisions.
An OLAP system is typically based on a multidimensional model, which allows users to easily select, explore, and view the data. An OLAP system generally provides the technology for creating and managing the databases. An OLAP system can have tools to discover relationships between data items by comparing the results of various OLAP queries.
Microsoft SQL Server version 7.0 includes a number of tools for data warehousing and online analytical processing, including Data Transformation Services (DTS) Designer and SQL Server OLAP Services. You can use DTS Designer to specify the workflow steps and transactions for combining multiple heterogeneous data sources into a data warehouse. You can then use OLAP Services to analyze the data, preaggregate data into multidimensional cubes for frequently asked queries, model data, create new views, and perform ad hoc sets of calculations.
On the Web
•
OLAP Council home page : http://www.olapcouncil.org
A power-management design initiative from Microsoft that combines innovation in PC hardware and software to produce a computer that is always on but appears to be off and that responds immediately when a user or application makes a request. For example, an incoming telephone call could wake the computer and start a TAPI-enabled application. OnNow is designed to make personal computers function like appliances in the sense that they respond instantly to user action instead of requiring a warm-up period or boot process. OnNow is based on the Advanced Configuration and Power Interface (ACPI) specification developed by Intel, Microsoft, and Toshiba.
Microsoft Windows 98 directs its power-management functions through the OnNow system. Instead of having the system BIOS control the power state of the system devices and peripherals, OnNow lets the operating system control it. The operating system can place various devices in a sleep state to conserve power and wake them to full power instantly when a user or application issues a request. For OnNow to function as designed, the system must have peripherals and applications that support OnNow power-management functions and the system BIOS must support ACPI.
A free version of UNIX that is based on the BSD 4.4 operating system and is maintained and supported by a large community of developers. The OpenBSD project is headed by Theo de Raadt, a computer science graduate of the University of Calgary in Alberta, Canada. OpenBSD is widely viewed as one of the most secure UNIX platforms available; even its default installation is fairly hacker-proof. OpenBSD includes support for the Kerberos IV security protocol and Internet Protocol Security (IPSec). OpenBSD also supports binary emulation of most software written for other popular UNIX flavors, such as HP-UX, SunOS, Solaris (SVR4), Linux, and FreeBSD. The current release of the OpenBSD software is version 2.5.
On the Web
•
OpenBSD home page : http://www.openbsd.org
A Microsoft database technology that provides an application programming interface (API) that Microsoft Windows–based applications can use to access structured query language (SQL) databases (such as those created and managed with Microsoft SQL Server) over a network.
How It Works
Open database connectivity (ODBC) defines a call-level interface that lets applications access data in any database through the appropriate ODBC driver. The ODBC API allows applications to be independent of the database management systems (DBMS’s) that manage their source data.
The main components of ODBC are as follows:
ODBC API: A set of function calls, error codes, and SQL syntax that defines how data in a DBMS is accessed.
ODBC database drivers: Dynamic-link libraries (DLLs) that can process ODBC function calls for specific DBMS’s. ODBC drivers translate application calls to ODBC into calls that the specific DBMS can respond to.
ODBC Driver Manager: Loads the ODBC drivers that an application needs.
ODBC, which is based on SQL, provides interoperability by allowing an application to access different SQL DBMS’s by using a common set of code. Developers can thus build client/server database applications without having to pre-specify which DBMS’s will be used for the back end. ODBC uses database drivers to link applications to any ODBC-compliant DBMS. ODBC database drivers are available for more than 50 popular DBMS’s, including SQL Server, Microsoft Access, Microsoft FoxPro, Microsoft Excel, Paradox, dBase, and delimited text files.
With ODBC, applications are not tied to proprietary vendor APIs and can run independently of the underlying data communication protocols. Data can be sent and received in a format suitable for the application instead of being tailored for a vendor-specific DBMS.
You can configure ODBC by using the ODBC utility in Control Panel. This utility lets you define a data source name (DSN) for the database being accessed and drivers for accessing the database. To configure ODBC with this utility, you associate a DSN with an ODBC driver, which lets an application interact with a database that is located either on the local machine or on a network server.
A standard developed by Novell and Apple for defining the communication mechanism between network interface card (NIC) drivers and network protocols. Open Data-link Interface (ODI) allows multiple NICs to be bound to multiple protocols, similar to the network driver interface specification (NDIS) standard. ODI is a legacy standard that was defined primarily for the Internetwork Packet Exchange (IPX) protocol on Novell NetWare 2. x and 3. x networks. Microsoft’s NWLink IPX/SPX-Compatible Transport supports ODI for backward compatibility.
A link state routing protocol that is used to exchange routing information between dynamic routers. Open Shortest Path First (OSPF) is an Interior Gateway Protocol (IGP) that is used mainly in larger TCP/IP internetworks and within autonomous systems of the Internet. OSPF is more efficient in terms of network overhead than the Routing Information Protocol (RIP), but it is considerably more complex to plan and implement in an enterprise.
How It Works
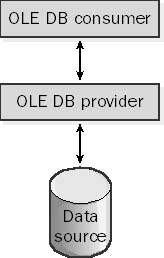
OSPF-enabled routers use the Shortest Path First (SPF) algorithm to compute the shortest path between nodes on an internetwork. They create a map (or tree) called the link state database that describes the topology or structure of the router’s specific network area. Network areas are groups of networks connected using OSPF-enabled routers that all have router interfaces for any of the networks included in the area. Areas typically have no more than about 30 or 40 routers and are connected to each other through a designated high-speed contiguous backbone area using area border routers (ABRs). OSPF areas simplify computation of link state information because the computational requirements of calculating link state information rise rapidly as the size and complexity of the network increase. With OSPF areas, each router need maintain only link state information about its own area and other areas connected to it, which improves the scalability of OSPF.
The link state information stored in the database (routing table) of each router includes cost information in addition to hop information. Administrators can configure routers in a complex mesh topology network so that specific paths are preferred over others. The SPF algorithm is used so that routing information can be quickly recalculated if routers are moved or if they go down. This feature is known as Fast Convergence. The SPF algorithm also ensures that the routing tables contain the shortest (least-cost) paths and that routing loops do not occur.
Graphic O-3. Open Shortest Path First (OSPF) Protocol.
The link state database of routing information is updated by advertisements using multicasting if a router goes down or if the structure of the network is reconfigured, and the database is used to calculate routes for delivering data over the network. Unlike the older RIP, OSPF uses multicasting to update only routing information, not the entire routing table. And unlike RIP-enabled routers, which broadcast routing information every 30 seconds, OSPF broadcasts changes only when they occur. These features substantially reduce inter-router network traffic compared to RIP and make OSPF a more efficient protocol than RIP for large internetworks.
NOTE
Microsoft Windows NT supports OSPF through the Routing and Remote Access Service (RRAS), which can be downloaded from the Microsoft Web site. OSPF will also be supported natively by Windows 2000.
TIP
When you design an OSPF-based internetwork, you should work from the top down—that is, you should first plan your autonomous system and how it will interact with other autonomous systems, and then you should subdivide the autonomous system into areas and then into individual networks. Try to map your IP address space and subnets to this hierarchy of areas and networks and assign each area a small set of network IDs that can be summarized as a small series of routes. Be sure that areas connect to each other through your high-speed backbone area and not directly to each other. (In other words, avoid back doors.) Specify cost values that relate to the amount of traffic and hardware characteristics of each router.
An architectural model for open networking systems that was developed by the International Organization for Standardization (ISO) in Europe in 1974. The Open Systems Interconnection (OSI) reference model was intended as a basis for developing universally accepted networking protocols, but this initiative essentially failed for the following reasons:
The standards process was relatively closed compared with the open standards process used by the Internet Engineering Task Force (IETF) to develop the TCP/IP protocol suite.
The model was overly complex. Some functions (such as connectionless communication) were neglected, while others (such as error correction and flow control) were repeated at several layers.
The growth of the Internet and TCP/IP—a simpler, real-world protocol model—pushed the OSI reference model out.
The U.S government tried to require compliance with the OSI reference model for U.S. government networking solutions in the late 1980s by implementing standards called Government Open Systems Interconnection Profiles (GOSIPs). This effort was abandoned in 1995, however, and now few real-world implementations of OSI networking protocols exist outside of Europe.
The OSI reference model is best seen as an idealized model of the logical connections that must occur in order for network communication to take place. Most protocol suites used in the real world, such as TCP/IP, DECnet, and Systems Network Architecture (SNA), map somewhat loosely to the OSI reference model. The OSI model is a good starting point for understanding how various protocols within a protocol suite function and interact.
The OSI reference model has seven logical layers, as shown in the following table.
The OSI Reference Model
| Layer Number | Layer Name | Description |
| 7 | Application layer | Interfaces user applications with network functionality, controls how applications access the network, and generates error messages. Protocols at this level include HTTP, FTP, SMTP, and NFS. |
| 6 | Presentation layer | Translates data to be transmitted by applications into a format suitable for transport over the network. Redirector software, such as the Workstation service for Microsoft Windows NT, is located at this level. Network shells are also defined at this layer. |
| 5 | Session layer | Defines how connections can be established, maintained, and terminated. Also performs name resolution functions. |
| 4 | Transport layer | Sequences packets so that they can be reassembled at the destination in the proper order. Generates acknowledgments and retransmits packets. Assembles packets after they are received. |
| 3 | Network layer | Defines logical host addresses such as IP addresses, creates packet headers, and routes packets across an internetwork using routers and Layer 3 switches. Strips the headers from the packets at the receiving end. |
| 2 | Data-link layer | Specifies how data bits are grouped into frames, and specifies frame formats. Responsible for error correction, flow control, hardware addressing (such as MAC addresses), and how devices such as hubs, bridges, repeaters, and Layer 2 switches operate. The Project 802 specifications divide this layer into two sublayers, the logical link control (LLC) layer and the media access control (MAC) layer. |
| 1 | Physical layer | Defines network transmission media, signaling methods, bit synchronization, architecture (such as Ethernet or Token Ring), and cabling topologies. Defines how network interface cards (NICs) interact with the media (cabling). |
You can think of each layer as being logically connected to the same layer on a different computer on the network. For example, the application layer on one machine communicates with the application layer on another machine. But this communication is logical only; physical communication occurs when packets of data are sent down from the application layer of the transmitting computer, encapsulated with header information by each lower layer, and then put on the wire at the physical layer of the transmitting computer. After traveling along the wire, the packets are picked up by the physical layer of the receiving computer, passed up the seven layers while each layer strips off its associated header information, and then passed to the application layer of the receiving computer, where the receiving application can process the data.
See also application layer, data-link layer, network layer, physical layer, presentation layer, session layer, transport layer
A set of signaling rates designed for transmission over Synchronous Optical Network (SONET) networks. Optical carrier (OC-x) levels also apply to Asynchronous Transfer Mode (ATM) networks. The term “optical carrier” indicates that SONET runs over fiber-optic cabling. The following table shows some of the common OC-x transmission rates.
OC-x Transmission Rates
| Name | Rate |
| OC-1 | 51.85 Mbps |
| OC-3 | 155.52 Mbps |
| OC-12 | 622.08 Mbps |
| OC-24 | 1.244 Gbps |
| OC-48 | 2.488 Gbps |
| OC-192 | 9.952 Gbps |
NOTE
OC-1 is roughly equivalent to T3 in the T-carrier system. It is a standard SONET Synchronous Transport Signal (STS) transmission rate of 51.85 Mbps. This data transmission rate is known as STS-1. Higher data transmission rates (OC-3, OC-12, and so on) are multiplexed STS-1 transmissions. In other words, OC-3 is three times faster than OC-1 (STS-1).
A device for electrically isolating networking components that are joined by long runs of copper cabling. Opto isolators prevent ground loops from damaging networking components.
How It Works
When a network component or cable transmitting a signal is connected to one port on an opto isolator, the signal is converted briefly into light and then back into an electrical signal before exiting through the other port on the opto isolator. This brief metamorphosis from electric current into light and back again breaks the electrical connection between the two ports of the device, allowing the signal (alternating current) to flow but preventing direct current from flowing along the cable.
Opto isolators are commonly used in RS-232 serial connections between mainframe hosts and terminals connected by long cables. Opto isolation is typically built into line drivers for serial communication, so separate opto isolators are not required.
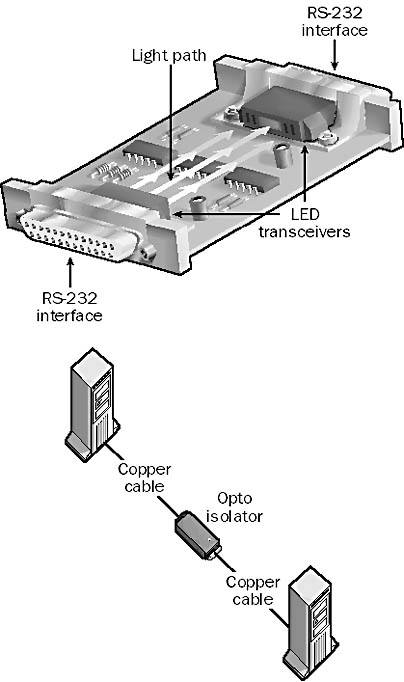
Graphic O-4. Opto isolator.
See also ground loop
Another name for the publication Trusted Computer Systems Evaluation Criteria (TCSEC), published by the National Computer Security Center (NCSC) of the U.S. Department of Defense. Orange Book standards are used to evaluate the security of both stand-alone and network operating systems (NOS’s). The current version of this publication dates from 1985. The Orange Book, which was named for its orange cover, is actually a part of a series of computer system security guidelines and standards that are collectively known as the Rainbow Series.
The Orange Book provides methods of assessing the security of a specific computer system, and it offers hardware and software manufacturers guidance on how to create products that can be certified as secure by the U.S. government and military.
For example, Microsoft Windows NT Server in certain configurations complies with the C2 (Controlled Access Protection) security standards outlined in the Orange Book. C2 is applied not to operating systems but to specifically tested physical computers running those operating systems. C2 is one of a family of security designations that the Orange Book applies to computer systems, which include the following:
D (Minimal Protection): For systems that were evaluated but failed.
C1 (Discretionary Security Protection): Provides separation between users and data by using access controls.
C2 (Controlled Access Protection): Adds user accountability to C1 in the form of logons, auditing, and other features.
B1 (Labeled Security Protection): Builds on C2 by including informal written security policies, data labeling, and mandatory access control.
B2 (Structured Protection): Builds on B1 by including formal written security policies, separation of critical and noncritical elements, and protection against covert entry.
B3 (Security Domains): Builds on B2 by including reference monitoring of all object access to ensure security, a designated security administrator, and system recovery procedures.
A1 (Verified Design): The same as B3, except security is verified by both testing and analysis of formal design. An A1 system is considered impenetrable to hostile attack.
A type of container object in Active Directory of Microsoft Windows 2000 that can contain other Active Directory objects.
How It Works
An organizational unit (OU) can contain other OUs, or it can contain specific objects, such as those listed here:
Users
Groups
Computers
File shares
Printers
Security policies
Applications
OUs make possible the hierarchical structure of Active Directory. Objects in the directory are grouped in tree-like structures for easier administration. OUs are displayed in Windows 2000 administrative consoles as folders, much like the folders in a file system that store individual files. OUs are logical groupings of users and resources in a domain; they simplify management of the domain by delegating administrative tasks to specific people.
OUs are often used to duplicate the organizational structure of the company within Active Directory. For example, a company might have OUs named Dev, Marketing, and Sales that represent the network resources of these three departments. OUs can also be assigned according to geographical criteria (New York, Los Angeles, and Detroit, for example) or by administrative function (Accounts, Shares, and Printers). When you run the Active Directory Installation Wizard to install Active Directory on a server running Windows 2000 (thus turning the server into a domain controller), a default hierarchy of OUs is created. This default hierarchy helps you begin administering Active Directory. It consists of the following OUs, which you can display by using Active Directory Users and Computers, a snap-in for Microsoft Management Console (MMC):
Builtin: Includes built-in security groups such as Administrators and Account Operators
Computers: Includes other computers in the domain
Users: Includes domain user objects
Domain Controllers: Includes the domain controllers in the domain
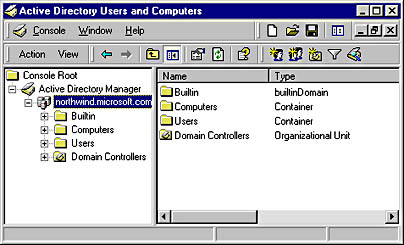
Graphic O-5. Organizational unit (OU).
The hierarchical structure of OUs in Active Directory also simplifies the task of querying Active Directory for information about network resources. OUs are useful in facilitating administration of Active Directory and therefore in the administration of resources on the network itself. Administrators use OUs to organize users and resources on the network, and to delegate administrative and other rights and permissions to users and groups. The administrator has full access rights on all objects in the directory and can assign permissions to various subtrees of OUs for appropriate users and groups. For any OU, the administrator can delegate either of the following rights to specific users and groups:
Complete administrative control: Full control over all objects in the OU
Limited administrative control: The ability to modify only certain aspects of objects contained in the OU
Access to objects in Active Directory is based on discretionary access control lists (DACLs), which offer a security model similar to that used in the NTFS file system. Because objects with similar security requirements are grouped into an OU, permissions assigned to the OU are inherited by all objects in the OU. You assign permissions to OUs and other objects by using Active Directory Users and Computers.
NOTE
If several domains are connected into a domain tree, each domain can have its own specifically designed hierarchy of OUs. The structures of domains within a domain tree are independent of one another. However, an OU can contain objects only from its own domain, not from any other domain within a domain tree.
OUs are not part of the namespace of a company, which in Windows 2000 is based on the Domain Name System (DNS). In other words, you can identify a Windows 2000 domain by using a DNS name such as northwind.microsoft.com, but you cannot identify OUs within the domain by using DNS names. However, you can specify OUs by using Lightweight Directory Access Protocol (LDAP) names.
You cannot create new OUs within the four default OUs previously listed. These default OUs simply get you started in administering your network.
TIP
To create new OUs in Active Directory, select the desired parent container in Active Directory Users and Computers, and choose Organizational Unit from the New submenu of the Action menu. You can also use the console toolbar. The only information you need to specify when you create a new OU is its name.
When you create an OU, you should consider who will own and manage it and who will be responsible for the following tasks:
Adding objects to or deleting objects from the OU
Modifying the values of attributes of objects in the OU
Managing permissions on the OU and its objects, and delegating the permissions to others
You can create OUs for groups of users who will be assigned similar permissions to network resources. You can also create separate OUs for permanent and temporary employees. You can group shared folders and printers with similar security requirements into OUs.
You should create OUs that are stable and will not change frequently, and you should avoid making the hierarchy of OUs too complicated. In a multidomain scenario with a domain tree, it is usually a good idea to make first-level OUs the same for all domains to provide consistency for the company’s network resources. First-level OUs typically represent the following:
Different geographical locations, such as countries or continents, or different functional locations, such as headquarters and branch offices. This is usually the best way to define first-level OUs.
Different types of network resources, such as users, printers, computers, and so on. This simplifies resource administration but might lead to too many first-level OUs.
Different business units, such as Sales, Support, and Management. Keep it flexible and broad enough so that if your company reorganizes, you won’t have to re-create everything.
Projects and cost centers.
Keep the entire structure of OUs fairly shallow—no more than two or three levels—to ensure good performance when users query Active Directory. A maximum of 10 levels of OUs is recommended.
You can use OUs in place of resource domains, which are used in Windows NT to simplify and centralize administration of network resources. You can also create domain trees with separate domains for resources. You should create new domains instead of OUs if you want to implement different security policies in different locations or branches of your company or in an extremely large enterprise. Otherwise, it is simpler to create only one domain and organize resources and administrative tasks using OUs within that domain.
The root or highest-level administrative unit in Microsoft Exchange Server, which is usually identified by the broadest name that can represent the enterprise’s business—the organization name cannot be changed without reinstalling all servers. An Exchange organization consists of a number of sites, each of which consists of one or more Exchange servers. Sites are connected by connectors such as a Site Connector or Dynamic RAS Connector. You can also use other connectors such as the Internet Mail Service Connector or X.400 Connector to provide messaging connectivity between your Exchange organization and a foreign mail system. Examples of such foreign mail systems include the following:
The collection of Simple Mail Transfer Protocol (SMTP) hosts on the Internet
A public or private X.400 message-handling system
Another Exchange organization
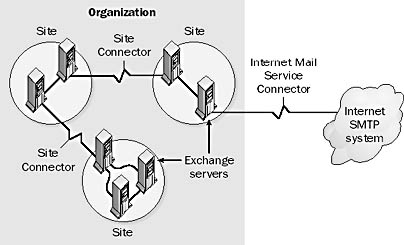
Graphic O-6. Organization in Microsoft Exchange Server.
In the Exchange directory hierarchy, which is displayed in the Exchange Administrator program, the Organization container contains
Site containers
Address book views
Public and system folders
Global address list
A 32-bit operating system originally developed by IBM and Microsoft as a replacement for MS-DOS. IBM later extended OS/2 to include both server and desktop versions. IBM’s current line of OS/2 software includes the OS/2 Warp Server, the OS/2 Advanced Warp Server, and the OS/2 Warp 4 client. OS/2 Warp in its various forms is a 32-bit preemptive multitasking operating system that supports application, file and print, groupware, and Web server configurations as well as desktop workstations. OS/2 Warp Server includes symmetric multiprocessing support and clustering technologies for high-availability server environments. OS/2 Warp Server supports most common networking protocols and all types of clients, including Microsoft Windows, Macintosh, and AIX clients.
On the Web
•
OS/2 Warp home page : http://www.software.ibm.com/os/warp
A component of the Microsoft Windows NT operating system running in user mode that supports the running of OS/2 1. x text-based applications on Windows NT. The OS/2 subsystem is rarely used and is not compatible with the OS/2 Presentation Manager graphical user interface.
In Windows 2000, OS/2 subsystem can be used only on a local computer, and can’t be used from a Terminal Server client computer.
See Open Systems Interconnection (OSI) reference model
See Open Shortest Path First (OSPF) Protocol
See organizational unit (OU)
A component of Microsoft Exchange Server that works with Internet Information Server (IIS) version 4 and Active Server Pages (ASP) technology to allow Exchange users to access their e-mail, address books, and public folder content using a standard Web browser such as Microsoft Internet Explorer. More generally, Microsoft Outlook Web Access allows administrators to publish Exchange services on the Web. It uses Hypertext Transfer Protocol (HTTP) on the client side and remote procedure calls (RPCs) on the server side.
A method of remotely managing the wide area network (WAN) telecommunications components of your network by using a secondary serial communication link. These devices are typically routers, switches, or Channel Service Unit/Data Service Units (CSU/DSUs) that establish and maintain WAN links to the corporate network. Devices that can be managed out-of-band usually have an RS-232 port or some other serial port for remote control of their functions.
How It Works
In a typical setup, a remote PC is connected by a modem through a phone line to a code-operated switch located at the office local area network (LAN). This switch controls networking and telecommunication devices such as routers, bridges, switches, CSUs, and even power supplies through their RS-232 serial connections. Alternatively, the modem might be connected directly to a remote modem connected to the device being managed. In either case, the result is a separate low-cost dial-up circuit connecting the administrator and the network devices that is independent of the main network connection, which is usually a more expensive T1 or other leased line. The administrator can thus access the WAN device from a remote location even when the WAN link itself is down, and can troubleshoot the problem from off-site. Out-of-band management (OBM) also allows administrators to access and configure WAN devices without disturbing the WAN link itself. In other words, OBM functions “out of the bandwidth.”

Graphic O-7. Out-of-band management (OBM).
For example, you can use OBM functions on a power supply to remotely reboot or reset your network devices when they go down. You can use out-of-band switches to select different serial interfaces remotely over a modem by issuing simple ASCII commands to different devices. You can even use OBM to remotely configure and control devices on your network. OBM devices are a useful part of a network disaster recovery plan.
For networking devices that you can configure and troubleshoot using out-of-band connections, you usually perform management tasks by connecting to a serial port (also called the setup port or configuration port) either locally with a cable or remotely through a modem. You usually use text-based commands from a terminal emulator program such as Windows HyperTerminal, which can emulate a VT100 terminal. You can often control access using passwords for extra security.
NOTE
OBM offers an advantage over in-band management systems such as Simple Network Management Protocol (SNMP) management systems. SNMP employs the network itself for communication, so if the WAN link goes down, the remote station cannot use SNMP to determine the problem because SNMP functions only if the WAN link is working.
OBM is often used as a backup system for in-band SNMP management, when the devices have limited SNMP support, or when the cost of an SNMP management system cannot be justified. You can often manage a device in-band by using a remote Telnet client for entering the same commands that are used in OBM.
TIP
You can often use out-of-band transmission so that a device that enters a problem state calls an administrator’s pager via a modem. The administrator can then dial in to the device remotely and correct the problem. Some network devices include built-in modems and data switches for remote OBM.
Any transmission technology in which signaling is separate from the data being transmitted. Out-of-band signaling uses one or more channels for transmitting data or voice information and one special out-of-band channel for performing signaling functions such as establishing and terminating the communication link, controlling flow, or transmitting error information. The out-of-band channel can be
A physically separate set of wires (such as pins 4 and 5 of an RS-232 cable, which perform flow control functions and do not carry data)
A multiplexed system in which bandwidth is divided into two or more channels within the same set of wires (such as Integrated Services Digital Network, in which the two B channels and one D channel are multiplexed onto the same set of wires)
The opposite of out-of-band is in-band, in which signaling information is sent over the same channel as the data transmission. Out-of-band transmission is usually considered a better choice than in-band transmission for the following reasons:
None of the valuable data bandwidth is used for signaling.
The data stream is not interrupted with signaling information.
The signaling information cannot be disrupted by the noise created by the data transmission.
Data transmission characters cannot accidentally (or purposefully) initiate control actions.
NOTE
Out-of-band circuits are often used for out-of-band management (OBM) of wide area network (WAN) devices. These are usually physically separate dial-up lines.
See also out-of-band management (OBM)
In the NTFS file system, the person ultimately responsible for the permissions assigned to a file, usually the creator of a file. By default, the owner of a file has permission to modify the object’s discretionary access control list (DACL) by granting users and groups permissions for various objects.
A file always has an owner. Ownership creates a trail of accountability for the file. The ownership of a file on an NTFS volume can be changed in two ways:
The user who owns the file, or any user who has full control permission on the file, can grant the NTFS take ownership permission to another user, thus allowing that user to take ownership of the file by using the file’s Security property sheet. Users can be allowed to take ownership of a file they do not own, but ownership cannot be assigned to them by other users (even the original owner or an administrator).
Members of the Administrators group can always take ownership of any file by using the Security property sheet. When an administrator takes ownership of a file, the Administrators group becomes the owner of the file, not the individual administrator.
In the Microsoft Windows 2000 operating system, objects in Active Directory also have owners. The user who creates an object in Active Directory becomes the object’s owner. The owner controls the permissions for the object and its attributes. Ownership of an object in Active Directory can be changed in ways similar to those for a file on an NTFS volume.