5.5 EMV(TM) certification chains
5.5 EMV ¢ certification chains
The EMV ¢ certification chain is presented in Figure 5.1.
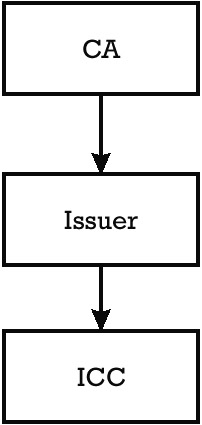
Figure 5.1: EMV ¢ certification chain.
The CA public key consists of the pair CA public key modulus and the CA public key exponent. This public key has to be stored in all the terminals that verify certificates originating from this CA, either directly or through the EMV ¢ certification chain.
There is no higher instance that can certify on this primary public key, and therefore, special precautions have to be taken for its authenticity and management as explained in Section 10 of Book 2 [1].
Furthermore, when an acquirer decides to participate in several EMV ¢ payment schemes, the terminal at the point of service has to store a database that keeps one record for each of the operational public keys of each CA accepted by the acquirer. A possible organization of this database is presented in Table 5.2. In this database a record corresponding to a CA public key is identified with two items:
-
The RID of the application accepting this CA;
-
An index allocated by the card association or payment system operator playing the role of the CA to each of its CA public keys, which could be operational at a certain moment. This index is kept in the terminal in the data object with tag 9F22.
| RID | CA Public Key Index (tag 9F22) | Algorithm Indicator | CA Public Key Modulus ” n CA | CA Public Key Exponent ” e CA |
|---|---|---|---|---|
| RID 1 | CA1 index 1 | AlgInd11 | CA1 public key (modulus ) 1 | CA1 public key exponent 1 |
| RID 1 | CA1 index 2 | AlgInd12 | CA1 public key (modulus) 2 | CA1 public key exponent 2 |
| RID 2 | CA2 index 1 | AlgInd21 | CA2 public key (modulus) 1 | CA2 public key exponent 1 |
|
|
|
|
|
|
| RID n | CA n index 1 | AlgInd n | CA n public key (modulus) 1 | CA n public key exponent 1 |
The record corresponding to a CA contains the modulus ( n CA ) and the public exponent ( e CA ) of each CA public key, as well as the algorithm indicator, which determines the type of algorithm that is used in conjunction with the CA public key for the verification of a certificate. In the example presented in Table 5.2, the certification authority CA1 has two operational CA public keys that are versioned with two different indexes, index 1 and index 2, respectively.
If a terminal needs to verify the Issuer Public Key Certificate received from a card to recover the corresponding issuer public key, the terminal also needs to receive the CA public key index (tag 8F) from the card.
Using this index, the terminal identifies in the CA public keys database the appropriate public key of the CA that shall be used for checking the Issuer Public Key Certificate. When this certificate verifies correctly, the terminal can obtain the issuer public key (issuer public key modulus and Issuer Public Key Exponent).
-
The terminal can use the issuer public key for verifying the authenticity of the certificate on the data personalized in the card by the issuer, which is referred to as the Signed Static Application Data (see Section 5.9). The terminal verifies this certificate in the case of off-line static data authentication (see Section 6.4.2).
-
Otherwise, the recovered issuer public key can be further used for verifying either an ICC Public Key Certificate or an ICC PIN Encipherment Public Key Certificate, which represents the second level of certificates in the EMV ¢ certification chain.
Once the ICC Public Key Certificate verifies correctly, the terminal can recover the ICC public key modulus and the ICC Public Key Exponent. Using this public key the terminal can verify any signature produced by the card with this key, which is the case of the off-line DDA (see Section 6.4.3).
If the ICC PIN Encipherment Public Key Certificate verifies correctly, the terminal can recover the ICC PIN encipherment public key modulus and the ICC PIN Encipherment Public Key Exponent. Using this public key, the terminal can produce a digital envelope and encrypt the PIN of the cardholder. Only the card can decrypt this digital envelope with the corresponding private key (see Section 6.6.5).
EAN: 2147483647
Pages: 131