Networking Routing Fundamentals
Table 2-4 lists the actual number of hosts and subnets for Class C IP addresses.
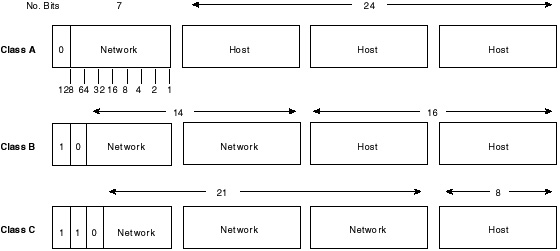
Figure 2-2 lays out the various IP address classes by network and host components.
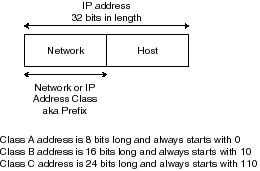
In most networks, the IP addresses assigned to that network have been broken into parts that logically relate to its different areas. For example, part of an IP address identifies a particular network, part identifies a subnet (that is, subnetwork), and part identifies a specific host within that subnetwork (that is, host). How IP Addresses Are ReadRouters examine the most significant or left-most bit of the first octet when determining the class of a network address. This technique of reading IP addresses (also known as the first octet rule) is discussed further as we define the different classes of addresses. The Role of IP AddressesIP uses a hierarchical addressing structure. A router simply sends the packet to the next hop in the route to reach its destination. For example, if a packet has a destination IP address of 172.24.50.10, the router will begin with the first octet (172) and search its routing tables for it. When a match is found, the router goes on to the next octet (24) until enough information is learned so that it can route the packet to its next destination. If the router does not have enough information to route the packet, then it will be dropped. Routers make their hierarchical decisions based upon the network and host components of an IP address, as demonstrated in Figure 2-3.
Another very good example of the hierarchical addressing technique used by routers is your phone number. For example, if the phone number 919-779-xxxx is dialed, the phone system knows that 919 is located in North Carolina, 779 is in the Raleigh area, and the last four numbers are assigned to a residence. An interesting side note here is that the telephone system is also running out of numbers, hence the implementation of the new toll-free extension, 888. Even in the use of phone numbers, you can see how technology has depleted the “bank” of possible numbers as a result of the use of modems, pagers, cellular phones, personal 800 numbers, and multiple phone lines in a residence. A router usually has an interface to which it connects. This interface will be assigned an IP address and subnet mask. Devices trying to reach a host within the network assigned to that interface will be routed through the interface. For example, a Token Ring interface has an IP address of 172.24.248.100. The router knows that packets going into or coming out of network 172.24.0.0 will need to interact with this interface. IP Subnet AddressingThe need for subnetting has resulted in the massive growth of networks in the past decade. As the available address space rapidly continues to shrink, network managers needed to use the existing space more efficiently; hence, subnetting was born. There are also some additional benefits to using subnetting have, such as:
To understand subnets better, just think of them as extensions of the network number. Essentially, you are reassigning part of what is “officially” the node address space to act as an additional network address. There are essentially three steps in assigning addresses in a network that has been subnetted:
In many organizations, subnets are used to divide one large network into a number of smaller networks. For example, the class B network used earlier (172.24.0.0) can be subdivided into 254 subnets:
This would provide 254 possible subnets, each having 254 hosts per subnet.
Subnet MaskingSubnet masks use the same format and representation technique as regular IP addresses. The subnet mask, however, has binary 1s in all bits specifying the host field. Essentially, a subnet mask is a 32-bit number that is applied to an IP address to override the default network/node address convention. The subnet mask also tells the router which octets of an IP address to pay attention to when comparing the destination address of a packet to its routing table. For example, for the subnet 172.24.1.0 you created to be properly configured, a mask must be applied of 255.255.255.0. This gives you a complete IP subnet address of 172.24.1.0 255.255.255.0. If you were to then apply this to an Ethernet interface of a router, and a packet came into the router with a destination address of 172.24.1.30, the router would be able to route the packet appropriately because it knows (via the assigned IP address and mask) that any packet destined for the network 172.24.1.0 is to be sent out the router’s Ethernet interface.
| ||||||||||||||||||||||||||||||||||
EAN: 2147483647
Pages: 200