Object Management, Ownership, and Inheritance
| Windows Server 2003 takes an object-based approach to describing resources and managing permissions. Objects that describe resources are defined on NTFS volumes and in Active Directory. With NTFS volumes , you can set permissions for files and folders. With Active Directory, you can set permissions for other types of objects, such as users, computers, and groups. You can use these permissions to control access with precision. Objects and Object ManagersWhether defined on an NTFS volume or in Active Directory, each type of object has an object manager and primary management tools. The object manager controls object settings and permissions. The primary management tools are the tools of choice for working with the object. Objects, their managers, and management tools are summarized in Table 14-2. Table 14-2. Windows Server 2003 Objects
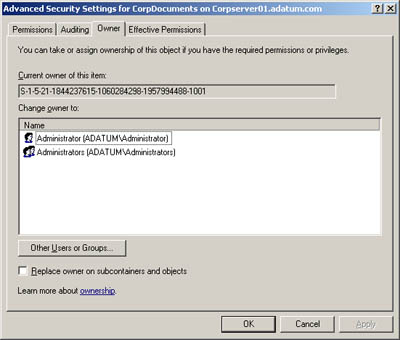
Object Ownership and TransferIt's important to understand the concept of object ownership. In Windows Server 2003, the object owner isn't necessarily the object's creator. Instead, the object owner is the person who has direct control over the object. Object owners can grant access permissions and give other users permission to take ownership of the object. As an administrator, you can take ownership of objects on the network. This ensures that authorized administrators can't be locked out of files, folders, printers, and other resources. Once you take ownership of files, however, you can't return ownership to the original owner (in most cases). This prevents administrators from accessing files and then trying to hide the fact. The way ownership is assigned initially depends on the location of the resource being created. In most cases, however, the Administrators group is listed as the current owner and the object's actual creator is listed as a person who can take ownership. Ownership can be transferred in several ways:
To take ownership of an object, follow these steps:
Object InheritanceObjects are defined using a parent-child structure. A parent object is a top-level object. A child object is an object defined below a parent object in the hierarchy. For example, the folder C:\ is the parent of the folders C:\data and C:\backups. Any subfolders created in C:\data or C:\ backups are children of these folders and grandchildren of C:\. Child objects can inherit permissions from parent objects. In fact, all Windows Server 2003 objects are created with inheritance enabled by default. This means that child objects automatically inherit the permissions of the parent. Because of this, the parent object permissions control access to the child object. If you want to change permissions on a child object, you must
To start or stop inheriting permissions from a parent object, follow these steps:
|
EAN: N/A
Pages: 141