Filtering on ICMP Packet Types
If you’ve ever attended one of my lectures on TCP/IP communications, then you know that ICMP is one of my favorite protocols. It provides a tremendous amount of information on the health of the network.[7]
Building an ICMP filter is pretty simple since it’s usually one of the many predefined protocol filters. What if you want to filter on a specific type of ICMP packet though? For example, you could build a filter for all ICMP Destination Unreachable packets. These packets indicate that a client may be misconfigured (set up with the wrong DNS server IP address, perhaps) or a service has been unloaded from a system (maybe the DHCP server is down right now).
ICMP packets use two fields to define the type of ICMP message that is being sent - they use a type field and a code field. These fields are adjacent to each other in the packet so we can just simply build one pattern for the specific type/code combination that we are interested in. We can then place our filter at the starting point where these two fields begin.
Figure 29 shows an ICMP packet - I’ve highlighted the type field so you can look at the hex window and see the adjacent code field for the Destination Unreachable - Port Unreachable packet. You can see that the code field follows immediately after type field.
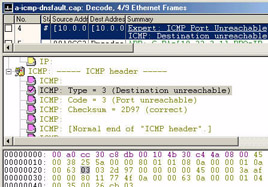
Figure 29: The type and code fields are adjacent - this means that we can build a single pattern that includes both field values.
Filtering on the value 0x0303 at protocol offset 14 (in hex) will ensure you catch all the ICMP Port Unreachable messages on the network. Figure 30 shows you what that pattern looks like.
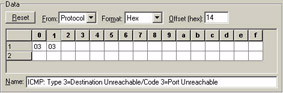
Figure 30: This is a great pattern filter -- you don’t even have to use AND/OR operands -- it’s the only pattern you want to match.
The following list indicates all the ICMP type and codes that you can filter on -- remember to combine the type and code fields to build a single pattern for each message. If no code is listed under a specific type number, it means that ICMP type doesn’t have any codes.
| # | Type (Code Listed Underneath) |
|---|---|
| 0 | Echo Reply |
| 3 | Destination Unreachable
|
| 4 | Source Quench |
| 5 | Redirect
|
| 6 | Alternate Host Address 0 Alternate Address for Host |
| 7 | Unassigned |
| 8 | Echo |
| 9 | Router Advertisement |
| 10 | Router Selection |
| 11 | Time Exceeded
|
| 12 | Parameter Problem
|
| 13 | Timestamp |
| 14 | Timestamp Reply |
| 15 | Information Request |
| 16 | Information Reply |
| 17 | Address Mask Request |
| 18 | Address Mask Reply |
Remember -- when you build these filters you need to convert over to hexadecimal if the analyzer vendor wants hex values. These are provided in decimal format.
| Note | For more information on ICMP, refer to RFC 792 and the “Analyzing and Troubleshooting TCP/IP” podbook. -- Laura |
[7]Go get a copy of the “Analyzing and Troubleshooting TCP/IP Networks” podbook. There is a lot of information on ICMP and you’ll certainly get other filter ideas based on the troubleshooting issues listed in the book.
EAN: 2147483647
Pages: 65