Security Events
As network hosts function, various events take place within them that change their state. In terms of security, these events (Fig. 2.1) can be represented by the following two components — action and target. Actions are steps taken by a specific subject (a user, process, etc.) in order to achieve a specific result. They include the following operations: reading, copying, modifying, deleting, and so on. A target represents a logical (an account, process, or data) or physical (a host, network, or component) system object.
User access to a file is an example of an event. When this event happens in accordance with security rules, it is considered to be a normal event. An event is an elementary unit used in current security tools. Although most security tools include a third parameter, namely, an event source, we will not include it in this description of a security model, because this parameter becomes significant only when a real attack exists.
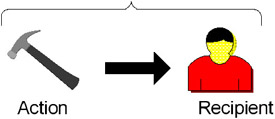
Fig. 2.1. A model of a security event
As soon as specific event violates security policy, it must be taken to be a part of an attack.
EAN: 2147483647
Pages: 152