Chapter 23: Security Policies and Exchange Server 2003
Overview
You might be wondering why a chapter on security policies is in a technical book. The reason is simple: you can’t effectively implement security for your Microsoft Exchange 2003 server until you implement security policies that instruct your organization about how to manage information held on that server. By defining what you are trying to secure and why, you can write information security policies that will form the foundation for the security technology you purchase and the electronic policies (e-policies) you create and implement. Figure 23-1 illustrates how information security policies lead to electronic policies. Figure 23-2 shows an example of how this would work.

Figure 23-1: How information security policies ultimately translate into electronic policies.
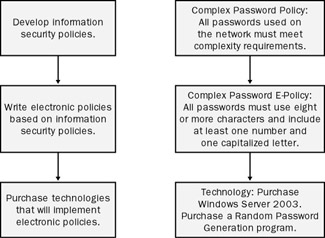
Figure 23-2: Password policy example.
| More Info | If you want an outstanding book on writing information security policies, please reference Information Security Policies Made Easy, by Charles Cresson Wood (PentaSafe). |
In most environments, the implementation of a security technology is the result of conversations between the IT department and other interested parties. What is often lacking in the initial planning stages is an explicit rationale for the security technology in the form of a written policy. Writing down your policy objectives and strategies will go a long way toward garnering support for your information security plan. In this chapter, we help you accomplish this by outlining the issues you need to consider when creating your information security policies and explaining why these issues are important.
EAN: 2147483647
Pages: 254