Authorization Example
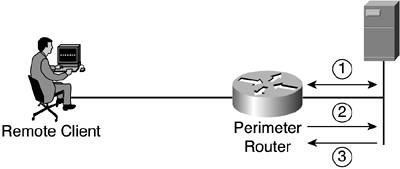
| You can clearly see the process of authorization using the same network example from earlier in the chapter. Figure 1-2 demonstrates a basic authorization process that can take place, in addition to the authentication process that is seen in the previous example. One difference you might note here is that in the authentication example, only a local authentication is discussed. In this authorization example, an AAA server is added, which includes authorizations. More detail on local authentication versus authentication using a server will be discussed in Chapter 3. Figure 1-2. Basic Authorization of FTP
In this situation, the following steps take place:
Again, the method list that is configured determines what authorization is to be performed. The configuration of a method list is discussed in Chapter 3; however, you might want to note that the configuration of a method list for authorization is the same as the method list configuration for authentication as well as accounting. |
EAN: 2147483647
Pages: 173
- Step 1.1 Install OpenSSH to Replace the Remote Access Protocols with Encrypted Versions
- Step 3.2 Use PuTTY / plink as a Command Line Replacement for telnet / rlogin
- Step 5.1 General Troubleshooting
- Step 6.2 Using Port Forwarding Within PuTTY to Read Your E-mail Securely
- Appendix - Sample sshd_config File