CCNA-Practice Test 2
Directions: For each of the following questions, select the choice that best answers the question or completes the statement.
| 1. | Your router discovers a remote network via a static route, EIGRP, and OSPF, and all the routing protocols are set to their default administrative distance. In this situation, which route will the router use to forward data to the newly discovered remote network?
| | ||||||||||||||||||||||||||||||||||||||
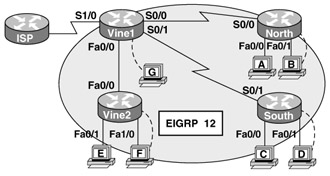
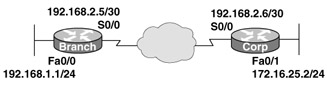
| 2. | Look at the following diagram. You've added another router called Vine2, but no routing updates are being exchanged between it and the pre-existing Vine1 router. You look into the issue and find that other interconnectivity and Internet access for all your existing locations throughout the corporate network are working great. What must you do to isolate the problem and tweak the router configurations so they can communicate fully?
| | ||||||||||||||||||||||||||||||||||||||
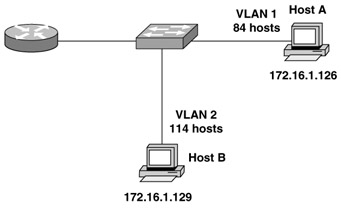
| 3. | Look at the following diagram. You can see that all your hosts are maintaining connectivity with each other. Choose three of the following that would be relevant to the addressing scheme likely used by this network:
| | ||||||||||||||||||||||||||||||||||||||
| 4. | Choose three of the following that accurately describe RIP.
| | ||||||||||||||||||||||||||||||||||||||
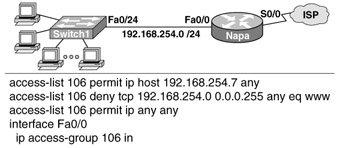
| 5. | Look at the following diagram. Which of the following will happen if you enter these command lines into the router?
Napa(config)# interface FastEthernet 0/0 Napa(config-if)# no ip access-group 106 in Napa(config-if)# interface Serial 0/0 Napa(config-if)# ip access-group 106 out
| | ||||||||||||||||||||||||||||||||||||||
| 6. | In a Spanning Tree topology, which of the following would you use to delimit the root port on each non-root switch?
| | ||||||||||||||||||||||||||||||||||||||
| 7. | Which of the following is the reason you configure port security on a switch?
| | ||||||||||||||||||||||||||||||||||||||
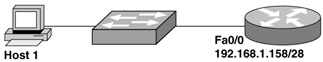
| 8. | Choose which IP address you would assign to Host 1 based on the following diagram.
| | ||||||||||||||||||||||||||||||||||||||
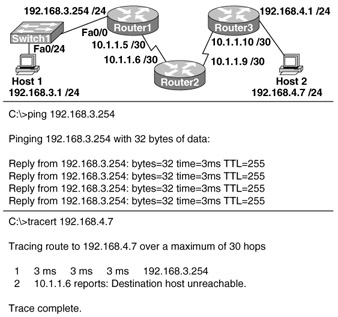
| 9. | While troubleshooting your internetwork's connection problems, you view Host1's output. Based on the following diagram, which of the following is the problem Host1's output is showing you?
| | ||||||||||||||||||||||||||||||||||||||
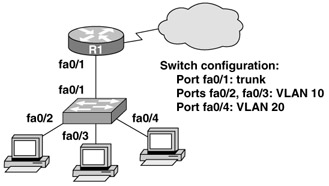
| 10. | Look at the following diagram. What's the best way to configure the FastEthernet0/1 ports on the 2950 model switches to achieve connectivity between all machines?
| | ||||||||||||||||||||||||||||||||||||||
| 11. | You need the 192.1.1.0/24 address to be subnetted over all three Ethernet networks that are attached to Vine1. Based on the following diagram, which of the following equals the greatest number of host addresses you can get using VLSM on all three networks collectively?
| | ||||||||||||||||||||||||||||||||||||||
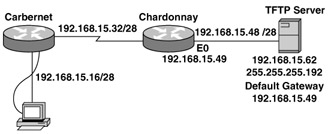
| 12. | You've installed a new router in the Cabernet location, but you can't back up the IOS image of this new router to a TFTP server at the Chardonnay location. Based on the following diagram, why is this happening?
| | ||||||||||||||||||||||||||||||||||||||
| 13. | Which of these situations would cause numerous copies of the same unicast frame to be transmitted over a switched LAN?
| | ||||||||||||||||||||||||||||||||||||||
| 14. | Which command would you use to configure a default route to a destination network that's not listed in the routing table?
| | ||||||||||||||||||||||||||||||||||||||
| 15. | Look at the following router output, and choose the answer that best describes what the term dynamic means in the output obtained via the show frame-relay map command: Code Listing 2-1
Vine#show frame-relay map Serial0/0 (up): ip 192.168.10.1 dlci 16 (0x64, 0x1840), dynamic Broadcast, status defined, active
| | ||||||||||||||||||||||||||||||||||||||
| 16. | The Winery Coop now has five branches throughout Napa and Sonoma, and they want to build a WAN to give them a completely meshed environment with a minimum of 512 kbps throughput. They also need the most cost-effective solution. Which WAN service should they choose?
| | ||||||||||||||||||||||||||||||||||||||
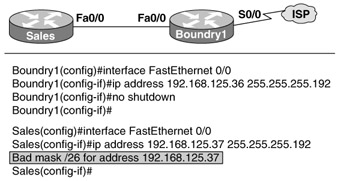
| 17. | Look at the following diagram. You're trying to configure the FastEthernet0/0 interfaces on the two interconnected routers, and you've configured Boundary1 without a hitch. But when you move on to configure the interface on the Sales router; you get the error message shown in the figure. Why is this happening?
| | ||||||||||||||||||||||||||||||||||||||
| 18. | Based on the following switch output, how would the switch have received the MAC table entry for 0012.7f4b.6882? Code Listing 2-2
Switch#sh mac address-table Mac Address Table ------------------------------------------- Vlan Mac Address Type Ports ---- ----------- -------- ----- All 0005.dccb.d740 STATIC CPU All 0100.0ccc.cccc STATIC CPU All 0100.0ccc.cccd STATIC CPU All 0100.0cdd.dddd STATIC CPU 1 000a.f467.9e80 DYNAMIC Fa0/11 1 0010.7b7f.c2b0 DYNAMIC Fa0/11 1 0012.7f4b.6880 DYNAMIC Fa0/11 1 0012.7f4b.6881 DYNAMIC Fa0/11 1 0012.7f4b.6882 DYNAMIC Fa0/11 1 0030.80dc.460b DYNAMIC Fa0/11 1 0030.9492.a5dd DYNAMIC Fa0/2 1 00d0.58ad.05f4 DYNAMIC Fa0/1 Total Mac Addresses for this criterion: 12 Switch#
| | ||||||||||||||||||||||||||||||||||||||
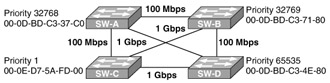
| 19. | Look at the following diagram. From what you see there, which of the following switches will be elected root bridge, and why?
| | ||||||||||||||||||||||||||||||||||||||
| 20. | You're adding a new router into an OSPF network, and the networks connected to your new router aren't showing up in the routing tables of the other OSPF routers. You have the subnets 10.10.10.0/24 and 10.11.11.0/24. What will your OSPF configuration be if you want to create one network entry and place both subnets into area 0?
| | ||||||||||||||||||||||||||||||||||||||
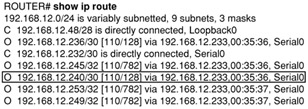
| 21. | Looking at the following output, what two things would you expect to discover in the line of show ip route output?
R 192.168.10.32 [120/3] via 192.168.10.17 00:00:23
| | ||||||||||||||||||||||||||||||||||||||
| 22. | You need to keep the hosts with the subnet address 172.16.24.0/21 in the VLAN from accessing telnet services. Which of the following would provide the missing answers in this command? (Choose three.)
access-list 110 deny protocol 172.16.24.0 mask any eq port
| | ||||||||||||||||||||||||||||||||||||||
| 23. | Why would you use this command?
ip route 0.0.0.0 0.0.0.0 serial0/0
| | ||||||||||||||||||||||||||||||||||||||
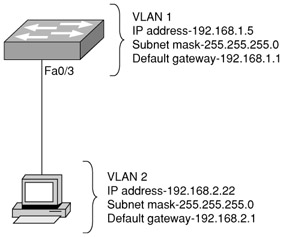
| 24. | Figure 2-11 shows a host connected to a switch port with a crossover cable. Everything is configured as shown in the figure and is correct. Why can't the host communicate with other hosts on the network?
| | ||||||||||||||||||||||||||||||||||||||
| 25. | Looking at the following diagram, why did VLAN connectivity issues begin to happen right after SwitchB was added to the network?
Figure 2-12 | | ||||||||||||||||||||||||||||||||||||||
| 26. | You're faced with reconfiguring a Catalyst 2950. Pick three steps that will guarantee the old configuration is erased.
| | ||||||||||||||||||||||||||||||||||||||
| 27. | If you were implementing VLSM on a network with a single Class C IP address, which subnet mask would you use to create the most effective point-to-point serial link?
| | ||||||||||||||||||||||||||||||||||||||
| 28. | You've subnetted your client's internetwork using 29 bits. You now need to configure an extended access list to control access to a whole subnetwork. To achieve this, which of the following wildcard masks should you use?
| | ||||||||||||||||||||||||||||||||||||||
| 29. | Look at following output, and pick the option that solves the problem of why Serial0/0 won't respond to a ping from a machine on the FastEthernet0/0 LAN. Code Listing 2-3
Napa#sh ip interface brief Interface IP-Address OK? Method Status Protocol Ethernet0/0 192.168.10.1 YES NVRAM up up Serial0/0 192.168.15.1 YES NVRAM administratively down down Serial0/1 192.168.16.1 YES NVRAM up up Serial0/2 unassigned YES NVRAM administratively down down Router#
| | ||||||||||||||||||||||||||||||||||||||
| 30. | You've configured a router three different times. You tested each configuration and successfully saved each of them to NVRAM using the copy running-config startup-config command. Then, you typed in the reload command. But now, when the router restarts, it looks as though it's got the default blank configuration. What's causing this?
| | ||||||||||||||||||||||||||||||||||||||
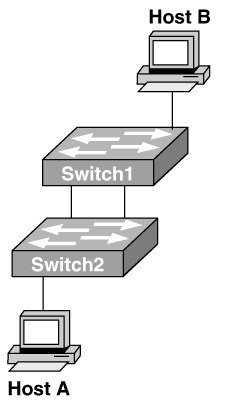
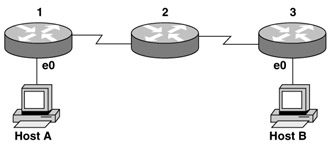
| 31. | Look at the following diagram. Host A sends an ARP request for the MAC address of Host B, and the network's performance practically grinds to a halt. The switches reveal a huge number of broadcast frames. What's causing this?
| | ||||||||||||||||||||||||||||||||||||||
| 32. | Why is a default route important?
| | ||||||||||||||||||||||||||||||||||||||
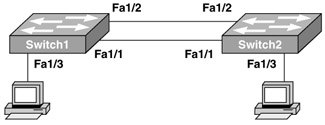
| 33. | Based on the following diagram, choose two options that describe ports that can safely be configured with PortFast:
| | ||||||||||||||||||||||||||||||||||||||
| 34. | The steps in PPP session establishment occur in a specific order. Choose the correct order from these alternatives:
| | ||||||||||||||||||||||||||||||||||||||
| 35. | Look at the following diagram. You've configured this internetwork as shown, and it appears that routing has been configured improperly. Of the following configuration options, which one will give hosts on the Branch LAN access to resources on the Corp LAN with the most efficient use of bandwidth and the least burden on router processing?
| | ||||||||||||||||||||||||||||||||||||||
| 36. | The local router's routing has been enabled with these commands: Code Listing 2-4
Local(config)# ip route 0.0.0.0 0.0.0.0 192.168.10.1 Local(config)# ip route 172.16.0.0 255.255.255.0 192.168.20.2 Local(config)# ip route 172.16.0.0 255.255.0.0 192.168.30.3 Match the destination IP address in the left column to the proper next hop address on the right:
| | ||||||||||||||||||||||||||||||||||||||
| 37. | Choose two of the following options that accurately describe the tasks that the OSPF Hello protocol performs:
| | ||||||||||||||||||||||||||||||||||||||
| 38. | Which type of EIGRP route entry describes a feasible successor?
| | ||||||||||||||||||||||||||||||||||||||
| 39. | What does a Layer 2 switch do if it receives a frame with a destination MAC address that is not found in its MAC address table?
| | ||||||||||||||||||||||||||||||||||||||
| 40. | You want the phrase "Unauthorized access prohibited!" to show up before the login prompt when a Telnet session to a router is attempted. Choose the command that you would use to achieve this.
| | ||||||||||||||||||||||||||||||||||||||
| 41. | A network administrator issues the ping 192.168.2.5 command and successfully tests connectivity to a host that has been newly connected to the network. Which protocols were used during the test? (Choose two.)
| | ||||||||||||||||||||||||||||||||||||||
| 42. | You've created the following access list and applied it to an interface. Which of the following are denied based on the access list? (Choose two.) Code Listing 2-5
access-list 107 deny tcp 207.16.12.0 0.0.3.255 any eq http access-list 107 permit ip any any
| | ||||||||||||||||||||||||||||||||||||||
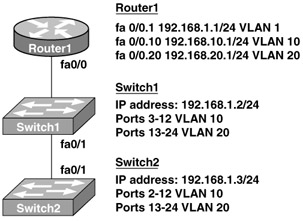
| 43. | Look at both the topology and configuration illustrated in the following diagram. Based on the fact that the router is configured to allow communication between the VLANs, choose the three IOS commands you need to configure switch port fa0/1 and establish a link with router R1 using the IEEE standard protocol:
| | ||||||||||||||||||||||||||||||||||||||
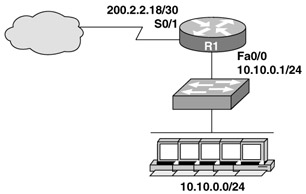
| 44. | Look at the following diagram. You want to use NAT in that network, so choose the two commands you can use to apply NAT configuration to the correct interfaces:
| | ||||||||||||||||||||||||||||||||||||||
| 45. | Match the cable type in the left column to the task for which it's best used, in the right column:
| | ||||||||||||||||||||||||||||||||||||||
| 46. | Look at the following diagram. You want Host A to communicate with Host B, but the e0 interface on router 3 is down. Choose the two events that will occur:
| | ||||||||||||||||||||||||||||||||||||||
| 47. | You view the code listing below. What does the 128 refer to in the router output? Code Listing 2-6
| | ||||||||||||||||||||||||||||||||||||||
| 48. | Choose three of the following options that accurately describe OSPF routing areas:
| | ||||||||||||||||||||||||||||||||||||||
| 49. | Choose the three services that use TCP:
| | ||||||||||||||||||||||||||||||||||||||
| 50. | By analyzing the following diagram, you're trying to understand how the Acme Corporation works. You can see that the server in VLAN4 supplies all resources required by the user hosts in the other VLANs. Choose the three interfaces that are access ports:
| | ||||||||||||||||||||||||||||||||||||||
| 51. | What is the subnetwork number of a host with an IP address of 172.16.210.0/22?
| | ||||||||||||||||||||||||||||||||||||||
| 52. | When setting up Frame Relay for point-to-point subinterfaces, which of the following must not be configured?
| | ||||||||||||||||||||||||||||||||||||||
| 53. | What is the purpose of the OSPF router ID in a DR/BDR election?
| | ||||||||||||||||||||||||||||||||||||||
| 54. | Which of the following is true concerning Frame Relay multipoint subinterfaces?
| | ||||||||||||||||||||||||||||||||||||||
| 55. | A network administrator wants to control which user hosts can access the network based on their MAC address. What will prevent workstations with unauthorized MAC addresses from connecting to the network through a switch?
| |
Answers
| 1. | A Explanation: A. Administrative Distance (AD) is the value a router uses to differentiate between routing information. Each routing protocol is given a value; a static route has the best AD with 1 (the lower the better; only a directly connected network is better with 0). | ||||||||||||||||||
| 2. | C Explanation: C. EIGRP (as well as IGRP) uses an autonomous system (AS) number in the routing configuration. As long as you use the same number on all your routers, they will exchange routing information. If they do not use the same AS number, they will not exchange information. In addition, the network statements are configured in a classful manner, which means all default host bits are off. For example, if you have a subnet of 10.10.16.0/28, the network statement under EIGRP would be 10.0.0.0. | ||||||||||||||||||
| 3. | B, C, F Explanation: B, C, F. The network shown in the figure has two VLANs configured; for the hosts in each VLAN to communicate, the router must be configured with subinterfaces, one for each VLAN. The block size in use is 128, so the mask is a /25 or 255.255.255.128. | ||||||||||||||||||
| 4. | A, B, F Explanation: A, B, F. RIPv1 is a classful routing protocols, which means all masks on every host in the network must be exactly the same. RIPv1 send broadcasts, and RIPv2 uses multicast: 224.0.0.9. RIP has many loop-avoidance mechanisms, some of which are split-horizon and hold-down timers. Others include route poison, setting infinity, and triggered updates. RIP v2 supports authentication as well; v1 does not. | ||||||||||||||||||
| 5. | A Explanation: A. The lines added to the ACL will be placed at the end of the access list, after the permit ip any any command line, which has no effect on denying packets. | ||||||||||||||||||
| 6. | A Explanation: A. Path cost is the first value that is used to determine which port should be blocking or forwarding. If path cost does not differentiate, then bridge id and port id can be used. | ||||||||||||||||||
| 7. | C Explanation: C. Port security can prevent unauthorized hosts from accessing the LAN. It can be configured with a maximum number of MAC addresses per port, or to allow only specifically configured MAC access. | ||||||||||||||||||
| 8. | C Explanation: C. The router is configured with the 192.168.1.158/28 address, which is the last valid host ID in the 192.168.1.144 subnet. The broadcast address for the subnet is 192.168.1.159, so the only valid host is 192.168.1.145. | ||||||||||||||||||
| 9. | A Explanation: A. Host1 can ping the default gateway, and traceroute does get to Router2, however, the packets cannot get past Router2, so this indicates a routing problem with Router2. | ||||||||||||||||||
| 10. | B Explanation: B. The cable between the switches needs to be a crossover cable, but they also need to be configured as a trunk port because multiple VLANs are configured on the switches. | ||||||||||||||||||
| 11. | E Explanation: E. Since you can VLSM this network, you can use one network of /25 and two /26 networks. That is 126 hosts and two 62 hosts. Add them up and that is 250 hosts. | ||||||||||||||||||
| 12. | B Explanation: B. The subnet mask on the TFTP is wrong. It should be 255.255.255.240, which is a /28. | ||||||||||||||||||
| 13. | D Explanation: D. If you have switches connected with dual links, and STP is not running, then you will have broadcast storms, multiple frame copies, and MAC table instability. | ||||||||||||||||||
| 14. | D Explanation: D. The ip route command can be used for a couple of different reasons: to set a static route to a network, and to set a default route. Here, a default route is being set. The syntax for the command includes the ip route command followed by the network and subnet mask being added. In this case, the fields are filled with zeros to indicate any network or default. The last field is the next hop address where the router must send packets to deliver them to the listed network. | ||||||||||||||||||
| 15. | E Explanation: E. Inverse ARP is the automatic process of finding a DLCI from a known IP address. If this function is not available, then the mapping of the DLCI to the IP address must be done manually through the frame-relay map command. | ||||||||||||||||||
| 16. | A Explanation: A. The bandwidth requirement and the fact that it is to be cost effective make Frame Relay the only real choice. | ||||||||||||||||||
| 17. | B Explanation: B. The router will not accept the IP address and mask without the ip subnet-zero command configured. This command allows the router to use the 0 subnet of a network that has been subnetted. | ||||||||||||||||||
| 18. | A Explanation: A. The best answer is that the MAC address was forwarded from another switch, because port Fa0/11 has many MAC addresses associated with it. | ||||||||||||||||||
| 19. | A Explanation: A. SW-A will become the root bridge because it has the lowest bridge ID, which is a combination of MAC address and priority. In this case, lowest MAC address becomes the root. Even though SW-C says it has a priority of 1; that is not possible. The lowest priority that can be set on a switch is 4096. | ||||||||||||||||||
| 20. | D Explanation: D. Although answer C is close to being correct, only answer D is correct, because you must have a space after the command area before listing the associated area. | ||||||||||||||||||
| 21. | D, E Explanation: D, E. The router output is a RIP entry in a routing table. The default administrative distance of RIP is 120, and the 120/3 means that the default AD of 120 is being used and the network in the table is three hops away. | ||||||||||||||||||
| 22. | A, D, F Explanation: A, D, F. To answer this question, you must know what a /21 is. A /21 is 255.255.248.0, which is a block size of 8, wildcard of 7, in the third octet (wildcards are always one less then the block size). Telnet uses TCP at the Transport layer and is well-known port number 23. | ||||||||||||||||||
| 23. | D Explanation: D. The ip route command with all zeros is a default route. Any traffic without a specific route will be sent out the interface specified at the end of the command. A next hop can also be used with the command instead of the exit interface. | ||||||||||||||||||
| 24. | B Explanation: B. Host C's address is on the wrong network. It is on the 13 network, whereas its current IP is on the 14 network. | ||||||||||||||||||
| 25. | B Explanation: B. If the revision number of the new switch is higher, the other switches will begin taking the new switch's update, which could cause connectivity problems. | ||||||||||||||||||
| 26. | B, C, E Explanation: B, C, E. A typical router can be set back to factory defaults by erasing the startup-config in NVRAM and then reloading the device. However, a switch keeps the VLAN database in Flash, and that must also be deleted on a switch to set it back to factory defaults. | ||||||||||||||||||
| 27. | D Explanation: D. A /30 or 255.255.255.252 provides only two hosts, regardless of the class of address, which is perfect for a point-to-point link. | ||||||||||||||||||
| 28. | E Explanation: E. First, you must know what a /29 is. The mask is 255.255.255.248, which means the block size is 8 in the fourth octet. A wildcard is always one less than the block size, so the answer is 0.0.0.7. | ||||||||||||||||||
| 29. | A Explanation: A. If an interface is administratively down, this means the interface is not enabled and must be enabled with the no shutdown command. All interfaces on a router are shut down by default | ||||||||||||||||||
| 30. | C Explanation: C. The default configuration register is set to 0x2102. If this is changed, then the router will not boot the default setting of loading the IOS from flash and the configuration from NVRAM. | ||||||||||||||||||
| 31. | C Explanation: C. If STP is disabled on the switches, then broadcast storms, multiple frame copies, and MAC address table instability problems will occur. | ||||||||||||||||||
| 32. | C Explanation: C. The ip route command can be used for a couple of different reasons: to set a static route to a network, and to set a default route. The default route allows IP to send packets to remote networks that are not specifically listed in the routing table. | ||||||||||||||||||
| 33. | C, D Explanation: C, D. PortFast is a feature that allows a port on a switch to transition directly to forwarding. Only ports that have end stations and are not connected to other switches should be configured like this. | ||||||||||||||||||
| 34. | E Explanation: E. The steps included in a PPP session establishment are link establishment, optional authentication, and network layer protocol. | ||||||||||||||||||
| 35. | A Explanation: A. By using static routes instead of a routing protocol configured on each router, processing will be minimized. However, this can be done because the network is small. In a larger network, static routes would be difficult to maintain. | ||||||||||||||||||
| 36. |
Explanation:
This is a hard question, no doubt about that. The top route is a default route, so any destination IP address that doesn't match the second and third line will be sent to 192.168.10.1. The difference between the second and third lines is the subnet mask. The second static route has a /24 mask, which makes the third octet the subnet address. Because the third static route has a /16 mask, the third octet is not part of the subnet. Once you determine that the third octet has to be a 0 to match the second static route, the rest of the answers fall into place. | ||||||||||||||||||
| 37. | A, C Explanation: A, C. A router running a link-state protocol uses hello packets to dynamically find neighbors and form adjacencies. Once an adjacency has been formed, it uses link state advertisement (LSA) packets to exchange topology information and updates when changes occur. | ||||||||||||||||||
| 38. | C Explanation: C. A feasible successor is stored in EIGRP's topology table, which holds all links known in the autonomous system. A successor route is copied from the topology table and placed in the routing table, which is then used by IP to route packets. The feasible successor is the backup route to the successor route. | ||||||||||||||||||
| 39. | C Explanation: C. A LAN switch uses MAC addresses to segment the network into collision domains. The switch looks at the source MAC address of each frame received on a port and places this in a forward/filter table, also called the content addressable memory (CAM) table. If a frame is received and the destination hardware (MAC) address is not found in the CAM table, the frame will be sent out all ports except the port it was received on. | ||||||||||||||||||
| 40. | C Explanation: C. The banner motd command means "message of the day." This is an old Unix command, but it is still useful on routers to provide messages to users logging in either via the console port or through telnet to a router or switch. | ||||||||||||||||||
| 41. | A, E Explanation: A, E. The ping program uses ICMP echo request and ICMP echo reply packets to find out if a host is "alive" on the network. Of course, ARP is used to resolve IP-to-hardware addresses for sending frames on a local network. | ||||||||||||||||||
| 42. | C, D Explanation: C, D. The wildcard in the mask is the key to the answer. 0.0.3.255 means the third octet has a wildcard of 4. The 12 in the third octet means that the access list will match 12, 13, 14, and 15, which make C and D the answers. B is wrong because the port number is wrong. | ||||||||||||||||||
| 43. | A, C, F Explanation: A, C, F. To configure a switch port to communicate with a router and share VLAN information, first choose the interface; then set the encapsulation type, in this case 802.1q; and then set the port to trunk. That is the correct order of configuration. | ||||||||||||||||||
| 44. | B, C Explanation: B, C. This is a pretty simple question. It ask you how to configure the interfaces, not the actual NAT commands. The interface commands are "ip nat inside" and "ip nat outside" from interface configuration mode. | ||||||||||||||||||
| 45. |
Explanation:
A switch port (called an access port if it is a member of only one VLAN) directly attached to a router needs a straight-through cable. However, if you have a switch-to-switch connection, you need a crossover cable. A cable from a COM port connecting to a router or switch console port would use a rolled cable. | ||||||||||||||||||
| 46. | A, D Explanation: A, D. If the interface e0 of Router 3 goes down, Router 4 will send a destination unreachable message type to the transmitting host, in this cast Host A. | ||||||||||||||||||
| 47. | A Explanation: A. OSPF uses only bandwidth to determine the best path to a remote network. By calculating the entire path, OSPF determines the cost of the path, which is shown in the router output. | ||||||||||||||||||
| 48. | C, D, E Explanation: C, D, E. When configuring OSPF, you must have an area 0, which is also called the backbone area. This area may be assigned any number from 0 to 2.4 billion. You must have an area 0, according to the CCNA objectives, but you don't have to have multiple areas. All routers can be in area 0. | ||||||||||||||||||
| 49. | B, D, E Explanation: B, D, E. SMTP, FTP, and HTTP are Application layer protocols that use TCP at the Transport layer. DHCP, SNMP, and TFTP all use UDP at the Transport layer. | ||||||||||||||||||
| 50. | A, C, D Explanation: A, C, D. There are two types of ports on a switch: an access port and a trunk port. A switch port cannot be both types of ports. An access port means the switch port is part of one VLAN and is typically used for a host and/or phone. A trunk port is used to connect to other switches and to routers. | ||||||||||||||||||
| 51. | C Explanation: C. To answer this question, you must know what a /22 is. A /22 is 255.255.252.0. This is a block size of 4 in the third octet. You count in increments of 4 until you pass 210. The subnet is 208.0, and the broadcast address is 172.16.211.255. | ||||||||||||||||||
| 52. | C Explanation: C. When creating subinterfaces on a router, an IP address is not configured under the physical interface of the router. IP addresses can only be configured under the logical (subinterfaces) interfaces, or the network will not function. | ||||||||||||||||||
| 53. | C Explanation: C. When OSPF is configured on a router, a router identification (RID) is created by using the highest IP address on any active interface at the moment of OSPF startup. The RID can be changed by creating a loopback interface, also called a logical interface. This RID is used by routers to determine which router will be a designated router or backup designated router in a broadcast or nonbroadcast multi-access network. | ||||||||||||||||||
| 54. | C Explanation: C. Unlike Frame Relay point-to-point subinterfaces, multipoint subinterfaces use one subnet for all PVC connections. Point-to-point uses one subnet for each PVC. | ||||||||||||||||||
| 55. | B Explanation: B. Port security can help you manage your switched network by allowing you to filter by MAC address and controlling the number of MAC addresses allowed on each port. |