Managing Users
| We have mentioned users previously, but in this section we examine how the sysadmin can manage the users. Users must be created, assigned a UID, provided a home directory, provided an initial set of files for their home directory, and assigned to groups so that they can use the system resources securely and efficiently. The system administrator might elect to restrict a user's access not only to files, but to the amount of disk space they use, too. User Management ToolsUbuntu provides several command-line tools for managing users, but also provides graphical tools for such. Many experienced sysadmins prefer the command-line tools because they are quick and easy to use and they can be included in scripts if the sysadmin desires to script a repetitive task. Here are the most commonly used commands used to manage users:
Note The set of files initially used to populate a new user's home directory are kept in /etc/skel. This is convenient for the system administrator because any special files, links, or directories that need to be universally applied can be placed in /etc/skel and will be duplicated automatically with appropriate permissions for each new user. $ ls -al /etc/skel total 20 drwxr-xr-x 2 root root 4096 2006-04-27 04:18 . drwxr-xr-x 110 root root 4096 2006-05-31 21:24 .. -rw-r--r-- 1 root root 220 2006-04-21 23:51 .bash_logout -rw-r--r-- 1 root root 414 2006-04-21 23:51 .bash_profile -rw-r--r-- 1 root root 2227 2006-04-21 23:51 .bashrc lrwxrwxrwx 1 root root 26 2006-05-07 15:29 Examples ->\ /usr/share/example-content Each line provides the file permissions, the number of files housed under that file or directory name, the file owner, the file group, the file size, the creation date, and the filename. As you can see, root owns every file here, but the adduser command (a symbolic link to the actual command named useradd) copies everything in /etc/skel to the new home directory and resets file ownership and permissions to the new user. Certain user files might exist that the system administrator doesn't want the user to change; the permissions for those files in /home/username can be reset so that the user can read them but can't write to them.
Tip To lock a user out of his account, use the following command: # passwd -l username This prepends an ! (exclamation point, also called a bang) to the user's encrypted password; the command to reverse the process uses the -u option. This is a more elegant and preferred solution to the problem than the traditional UNIX way of manually editing the file.
Adding New UsersThe command-line approach to adding this user is actually quite simple and can be accomplished on a single line. In the example shown here, the sysadmin uses the useradd command to add the new user bernice. The command adduser (a variant found on some UNIX systems) is a symbolic link to useradd, so both commands work the same. In this example, we use the -p option to set the password the user requested; we use the -s to set his special shell, and the -u option to specify his UID. (If we create a user with the default settings, we do not need to use these options.) All we want to do can be accomplished on one line: # useradd bernice -p sTitcher -s /bin/zsh -u 507 The sysadmin can also use the graphical interface that Ubuntu provides, as shown in Figure 14.2. It is accessed as the Users and Groups item from the Administration menu. Here, the sysadmin is adding a new user to the system where user bernice uses the bash command shell. Figure 14.2. Adding a new user is simple. The GUI provides a more complete set of commands for user management than for group management.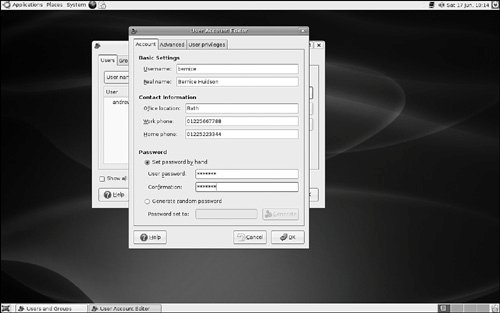 These are the steps we used to add the same account as shown in the preceding command, but using the graphical User Manager interface:
Note that the user is being manually assigned the UID of 1413 because that is her UID on another system machine that will be connected to this machine. Because the system only knows her as 1001 and not as bernice, the two machines would not recognize bernice as the same user if two different UIDs were assigned. Note A Linux username can be any alphanumeric combination that does not begin with a special character reserved for shell script use (see Chapter 15 for disallowed characters, mostly punctuation characters). In Chapter 5, we told you that usernames are typically the user's first name plus the first initial of her last name. That is a common practice on larger systems with many users because it makes life simpler for the sysadmin, but is neither a rule nor a requirement. Monitoring User Activity on the SystemMonitoring user activity is part of the sysadmin's duties and an essential task in tracking how system resources are being used. The w command tells the sysadmin who is logged in, where he is logged in, and what he is doing. No one can hide from the super user. The w command can be followed by a specific user's name to show only that user. The ac command provides information about the total connect time of a user measured in hours. It accesses the /var/log/wtmp file for the source of its information. The ac command proves most useful in shell scripts to generate reports on operating system usage for management review. Note that you have to install the acct package using either synaptic or apt-get Tip Interestingly, a phenomenon known as timewarp can occur in which an entry in the wtmp files jumps back into the past and ac shows unusual amounts of time accounted for users. Although this can be attributed to some innocuous factors having to do with the system clock, it is worthy of investigation by the sysadmin because it can also be the result of a security breach. The last command searches through the /var/log/wtmp file and lists all the users logged in and out since that file was first created. The user reboot exists so that you might know who has logged in since the last reboot. A companion to last is the command lastb, which shows all failed, or bad, logins. It is useful for determining whether a legitimate user is having trouble or a hacker is attempting access. Note The accounting system on your computer keeps track of usage user statistics and is kept in the current /var/log/wtmp file. That file is managed by the init and login processes. If you want to explore the depths of the accounting system, use the GNU info system: info accounting. |
EAN: 2147483647
Pages: 318